[Updated 8-Nov-2021]
The next step is to create an additional management server VM from the Server 2019 template. We use the VM built in this article for an additional infrastructure server. My Lab’s infrastructure VMs reside in my XenServer pool, as explained in the Introduction article. Building a server VM from the Server 2019 template was covered earlier.
From the introduction article, this is the VM we are building:
| Name | Description | IP Address |
| LabControlUp | ControlUp Management Server | 192.168.1.207 |
Before building the new server, we need to verify the hardware requirements for ControlUp.
Request Trial
ControlUp optimizes the digital experience with actionable insights captured through real-time observation. With accurate end-to-end analysis of the user’s digital journey, ControlUp enables IT admins to make faster decisions with actionable insights and enterprise-grade tools that troubleshoot and remediate user issues to deliver the best-in-class digital employee experience and productivity.
ControlUp monitoring uses three parts, the Real-time console, the Monitor node, and Agents.
- The ControlUp Real-Time console leverages the association and correlation logic of the real-time engine to generate aggregated views of multiple data sources. These powerful grids can be sorted by, grouped by, filtered by, or searched by any of the dozens of continuously updated real-time metrics.
- The ControlUp Monitor is a component principally equivalent to ControlUp Console, but without an interactive user interface. Once installed and started, ControlUp Monitor signs into your ControlUp organization and connects to your managed computers.
The Monitor starts receiving system information and performance updates from your organization, just like an additional ControlUp Console user. The primary difference between a Monitor and a Console is that the Monitor runs as a Windows Service 24/7, requiring no user interaction and allowing for continuous monitoring and auto-remediation of your environment.
- ControlUp agents allow communication with the Console and the Monitor.
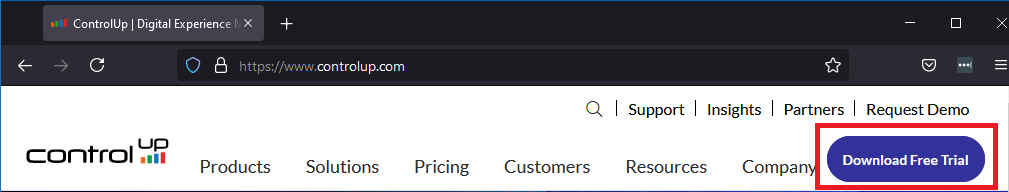
To receive a free trial of ControlUp, use your internet browser and browse to https://ControlUp.com/ and click on Download Free Trial, as shown in Figure 1.
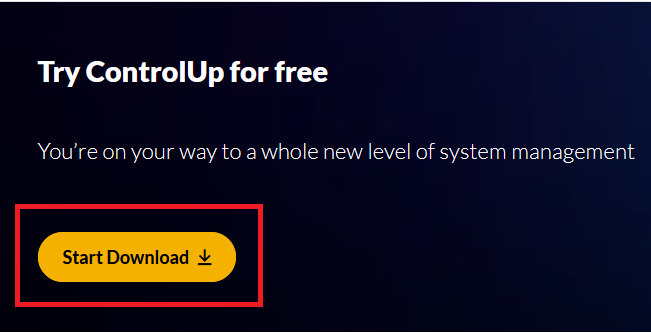
Click Start Download, as shown in Figure 2.
Here are the links needed with the information needed to build our ControlUp VM.
https://support.controlup.com/hc/en-us/articles/206501579-Hypervisor-Monitoring-Requirements (Covers Citrix XenServer)
https://support.controlup.com/hc/en-us/articles/360000532477-AV-Exclusions-for-ControlUp
We are building a ControlUp server to handle the small number of VMs used for the future Citrix Virtual Apps and Desktops and VMware Horizon article series. Since the Lab will have minimal Citrix and VMware infrastructure servers and a minimal number of virtual desktops, the requirements are minimal for the ControlUp server VM.
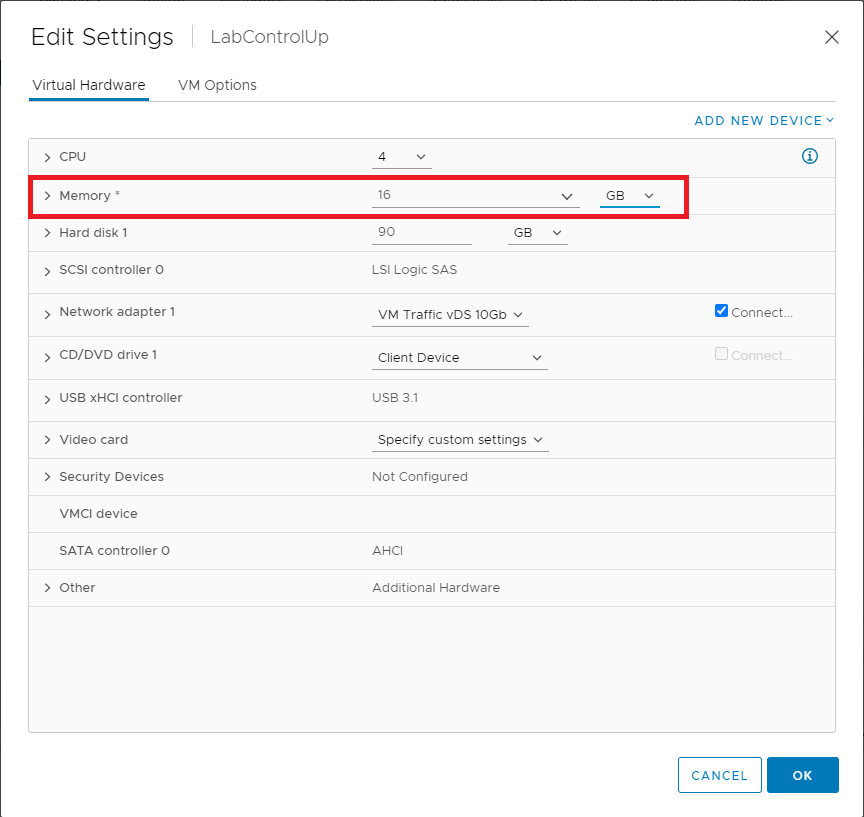
From this information, we learn the following about the ControlUp server’s VM:
- It needs a static IP address
- Increase the RAM to 16GB
- We run the Console and Monitor on one server. Since there is no local database, ControlUp caches monitoring results in the server’s RAM.
- Requires the installation of an additional internet browser
- We don’t use Internet Explorer 11 for anything
- Requires Windows firewall configuration
- Requires Windows Defender configuration
- Needs service accounts for VMware vCenter and Citrix XenCenter
- These service accounts are not required, but we use specific service accounts for specific purposes
Following the process used for the other lab servers built, create a new VM from the Server 2019 template and do not power it on.
Change RAM
VMware
In vCenter, right-click the LabControlUp VM, click Edit Settings…, and change the Memory settings, as shown in Figure 3.
Power on the VM, enter the required hostname, enter the required IP address information, and install Windows Updates. I also installed Google Chrome to use as my browser.
XenServer
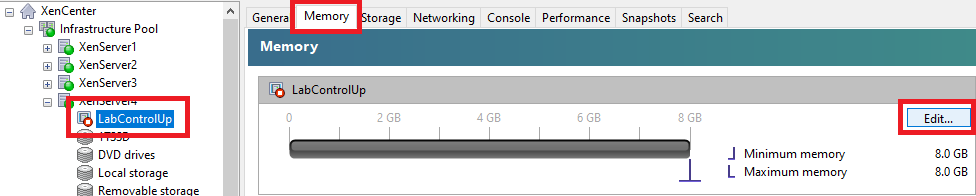
Select the LabControlUp VM, click the Memory tab, and click Edit…, as shown in Figure 4.
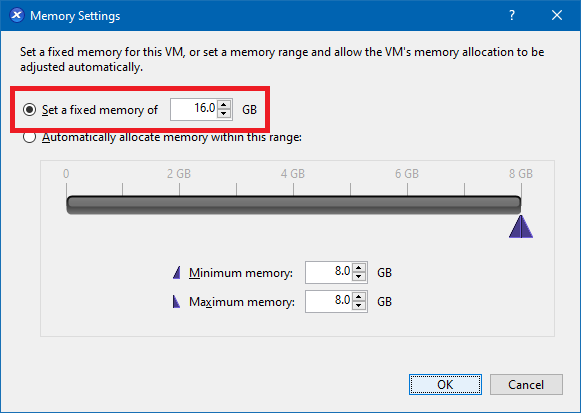
Select Set a fixed memory of and change the value to 16.0, as shown in Figure 5.
Power on the VM, enter the required hostname, enter the required IP address information, and install Windows Updates. I also installed Google Chrome to use as my browser.
Active Directory
Join Active Directory
First, we need to create an OU.
If you remember, when we created Active Directory in Part 14, I placed all my infrastructure servers in a specific OU.
Lab
Infrastructure
The ControlUp server is placed in an OU to apply GPOs for Windows Firewall and Windows Defender configurations.
Lab
Infrastructure
ControlUp
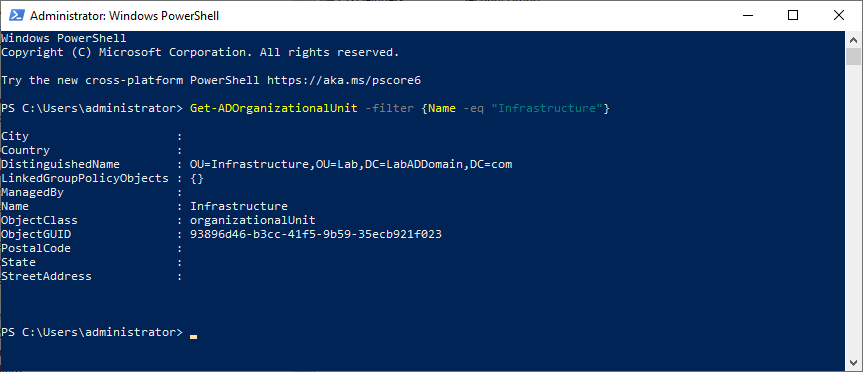
From the Lab’s management computer, start an elevated PowerShell session and type in the following, as shown in Figure 6.
Get-ADOrganizationalUnit -filter {Name -eq "Infrastructure"}
Create the ControlUp OU.
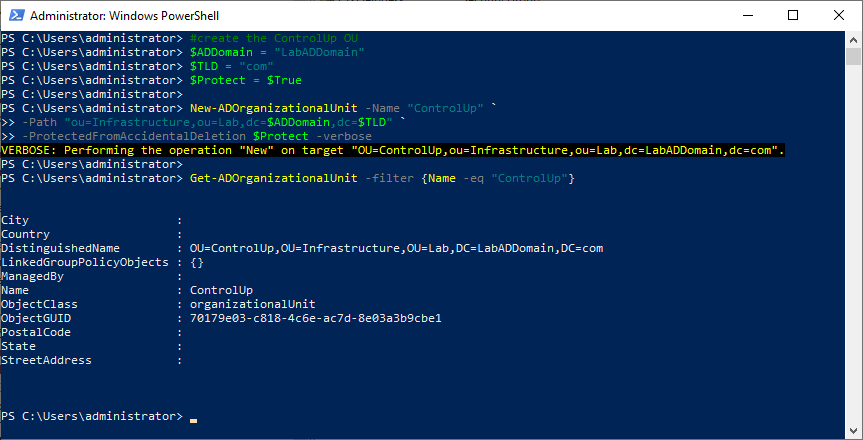
Copy and paste the following into the elevated PowerShell session and press Enter, as shown in Figure 7.
Remember to set the values you need.
Note: Lines may wrap
#create the ControlUp OU
$ADDomain = "LabADDomain"
$TLD = "com"
$Protect = $True
New-ADOrganizationalUnit -Name "ControlUp" `
-Path "ou=Infrastructure,ou=Lab,dc=$ADDomain,dc=$TLD" `
-ProtectedFromAccidentalDeletion $Protect -verbose
Get-ADOrganizationalUnit -filter {Name -eq "ControlUp"}
Copy the DistinguishedName property to the clipboard.
LabControlUp Server Work
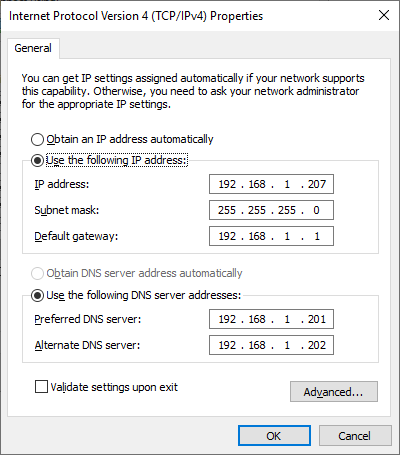
Verify that the server has a static IP address and uses the IP addresses of the domain controllers for the DNS servers, as shown in Figure 8.
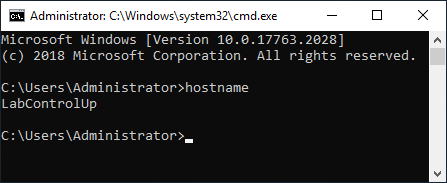
Verify that the server has the correct hostname, as shown in Figure 9.
Use mstsc to remote into the VM that is our ControlUp server.
Exit Server Manager and start an elevated PowerShell session.
Copy and paste the following into the elevated PowerShell session and press Enter. The process took less than the blink of an eye to happen, which is why there is no screenshot.
Remember to set the values you need.
Note: Lines may wrap
#Join the computer to the domain add-computer -Credential LabADDomain\Administrator ` -DomainName "LabADDomain.com" ` -OUPath "OU=ControlUp,OU=Infrastructure,OU=Lab,DC=LabADDomain,DC=com" ` -Force ` -Restart #server reboots
After the VM restarts, log in using the domain’s Administrator account and password.
Now to install the server certificate from the CA.
Save the following to a file name c:\CertFiles\computer-request.inf.
I want to thank Michael B. Smith for creating this INF file for me.
Use the data needed for your environment.
LabControlUp = the name of your ControlUp server
LabADDomain.com = your domain name
"LabCA\LabDomain CA Root" = the name of your CA server and the name of your CA.
;----------------- computer-request.inf -----------------
; LabControlUp.LabADDomain.com
;
; certreq -new computer-request.inf computer-request.req
; certreq -submit -config "LabCA\LabDomain CA Root" computer-request.req computer-request.cer
; certreq -accept -config "LabCA\LabDomain CA Root" computer-request.cer
;
[Version]
Signature="$Windows NT$"
[NewRequest]
Subject = "CN=LabControlUp.LabADDomain.com" ; replace with the FQDN of the File Server
FriendlyName = "Computer (Machine) for LabControlUp.LabADDomain.com"
KeyLength = 2048
; Can be 1024, 2048, 4096, 8192, or 16384.
; Larger key sizes are more secure, but have
; a greater impact on performance.
KeySpec = 1 ; AT_KEYEXCHANGE
Exportable = TRUE ; private-key is exportable
MachineKeySet = TRUE ; goes in machine store instead of user's personal store
SMIME = False ; cannot be used for signing S/MIME messages
PrivateKeyArchive = FALSE
HashAlgorithm = sha256 ; "certutil -oid 1 | findstr pwszName" -- gives a list (including sha1)
UserProtected = FALSE
UseExistingKeySet = FALSE ; we are not renewing a key that already exists
ProviderName = "Microsoft RSA SChannel Cryptographic Provider"
ProviderType = 12 ; for ProviderName and ProviderType, see "certutil -csplist"
RequestType = PKCS10 ; if empty or set to "CERT" then a self-signed cert is created
KeyUsage = 0xa0 ; 0xa0 - CERT_DIGITAL_SIGNATURE_KEY_USAGE + CERT_KEY_ENCIPHERMENT_KEY_USAGE
[EnhancedKeyUsageExtension]
OID=1.3.6.1.5.5.7.3.1 ; this is for Server Authentication - PKIX_KP_SERVER_AUTH
[Extensions]
; Note: 2.5.29.17 is the OID for a SAN extension.
2.5.29.17 = "{text}"
_continue_ = "dns=LabControlUp.LabADDomain.com"
[RequestAttributes]
CertificateTemplate = "Server Template"
;-----------------------------------------------
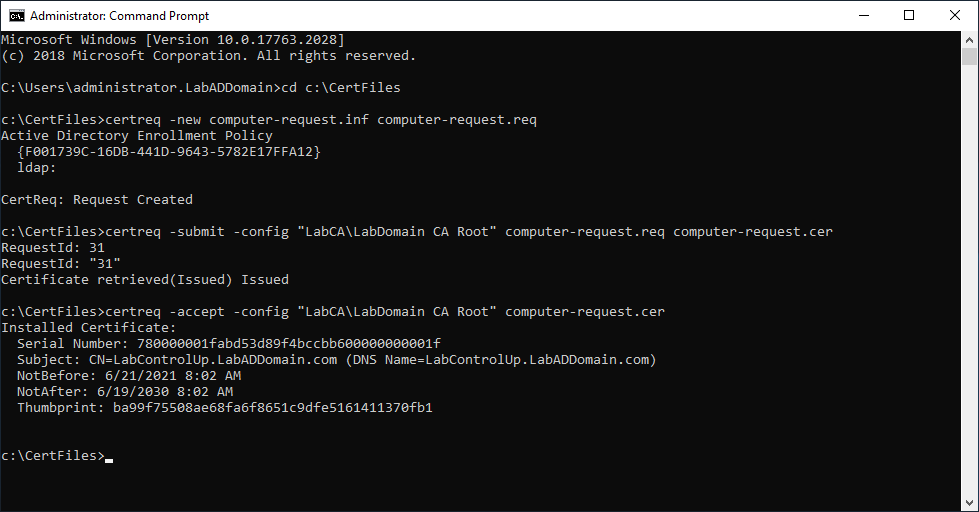
Open an elevated command prompt.
Type in cd c:\CertFiles and press Enter.
The three commands we need to run are at the top of the computer-request.inf file.
Type in notepad computer-request.inf and press Enter.
Copy the line certreq -new computer-request.inf computer-request.req, paste it in the elevated command prompt, and press Enter.
Copy the line certreq -submit -config “LabCA\LabDomain CA Root” computer-request.req computer-request.cer, paste it in the elevated command prompt, and press Enter.
Note: If you get a warning similar to the following, you can ignore the warning. The warning tells you that the certificate request validity period is past the lifetime of the CA’s root certificate lifespan.
Certificate retrieved(Issued)Issued The certificate validity period will be shorter than the Server Template Certificate Template specifies because the template validity period is longer than the maximum certificate validity period allowed by the CA. Consider renewing the CA certificate, reducing the template validity period, or increasing the registry validity period.
Copy the line certreq -accept -config “LabCA\LabDomain CA Root” computer-request.cer, paste it in the elevated command prompt, and press Enter.
Figure 10 shows the results of running the certificate request commands.
Create ControlUp Accounts
Additional vCenter Configuration
The vCenter Read-Only role created earlier is sufficient for all monitoring purposes. However, we want to use the built-in hypervisor-based VM power management functions. Therefore, we need to create a custom role based on the Read-Only role, adding the following permissions:
- In the Virtual Machine/Interaction category:
- Power Off
- Power On
- Reset
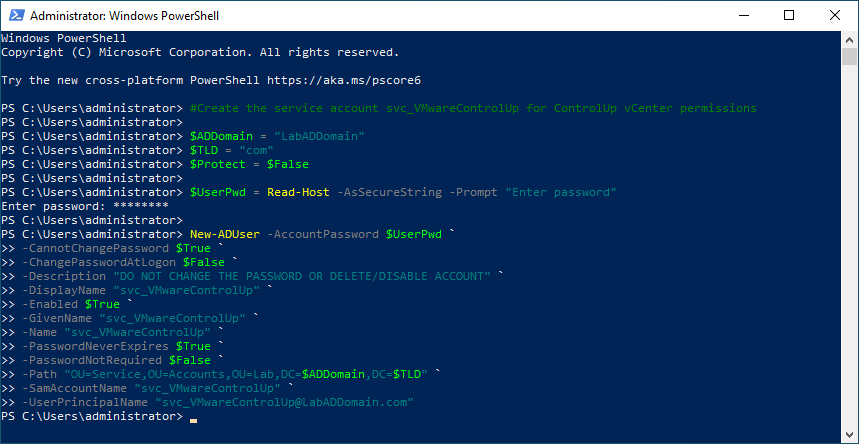
First, we need to create an AD service account to assign the vCenter Custom Role.
From the Lab’s management computer, start an elevated PowerShell session, copy and paste the following into the elevated PowerShell session, and press Enter, as shown in Figure 11.
Remember to set the values you need.
Note: Lines may wrap
#Create the service account svc_VMwareControlUp for ControlUp vCenter permissions $ADDomain = "LabADDomain" $TLD = "com" $Protect = $False $UserPwd = Read-Host -AsSecureString -Prompt "Enter password" New-ADUser -AccountPassword $UserPwd ` -CannotChangePassword $True ` -ChangePasswordAtLogon $False ` -Description "DO NOT CHANGE THE PASSWORD OR DELETE/DISABLE ACCOUNT" ` -DisplayName "svc_VMwareControlUp" ` -Enabled $True ` -GivenName "svc_VMwareControlUp" ` -Name "svc_VMwareControlUp" ` -PasswordNeverExpires $True ` -PasswordNotRequired $False ` -Path "OU=Service,OU=Accounts,OU=Lab,DC=$ADDomain,DC=$TLD" ` -SamAccountName "svc_VMwareControlUp" ` -UserPrincipalName "[email protected]"
Log in to vCenter.
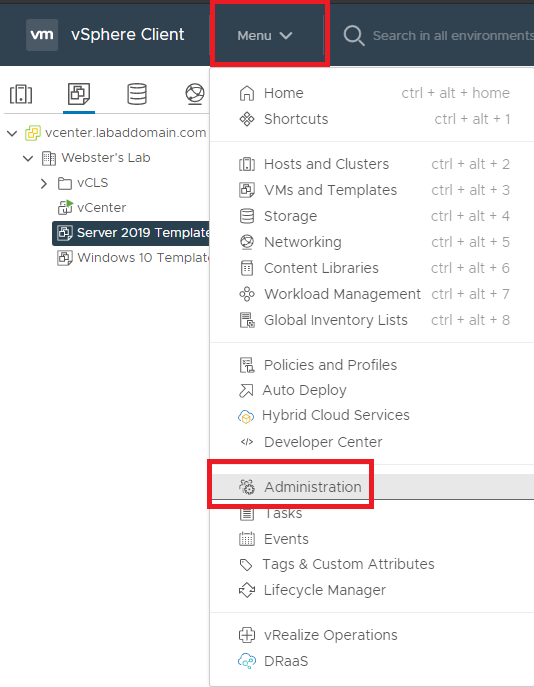
From the Menu dropdown, select Administration, as shown in Figure 12.
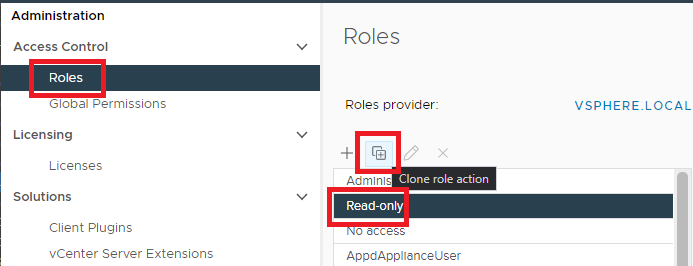
In Roles, click the Read-only role and click the Clone role action icon, as shown in Figure 13.
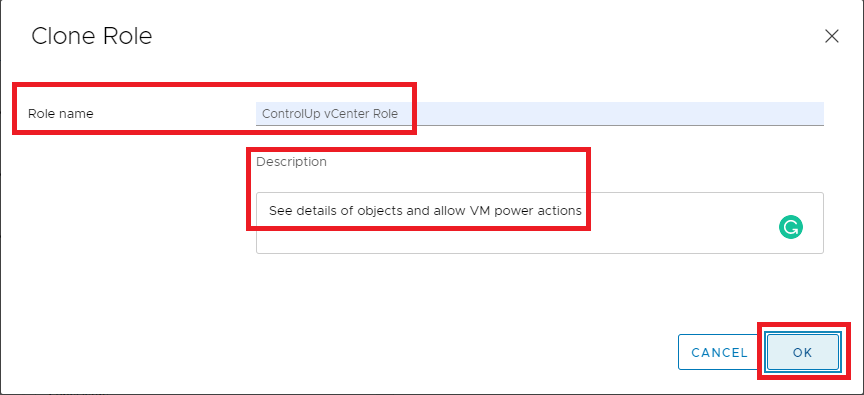
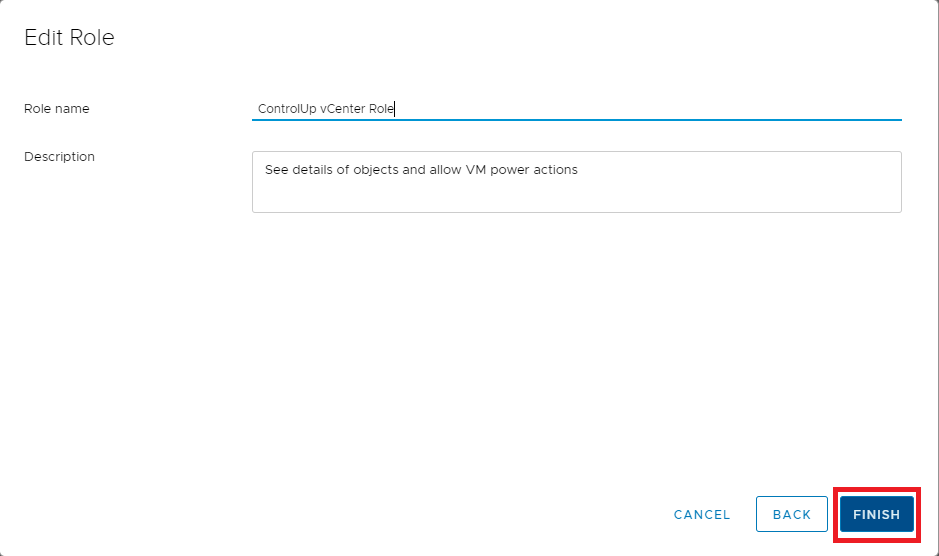
Enter a Role name, Description, and click OK, as shown in Figure 14.
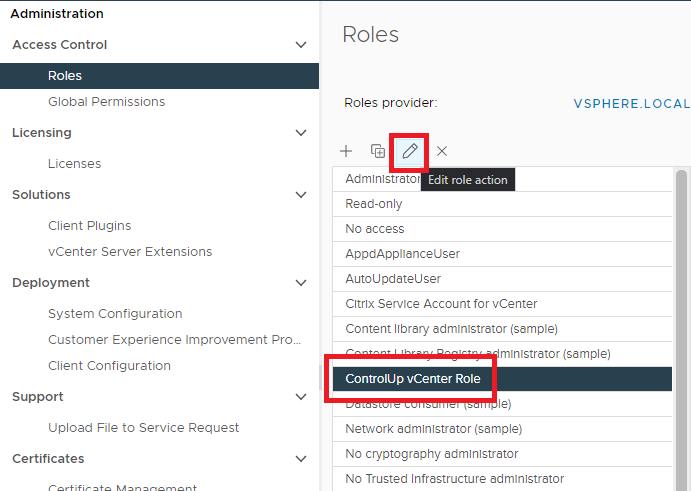
Click the new role and click the pencil Edit icon, as shown in Figure 15.
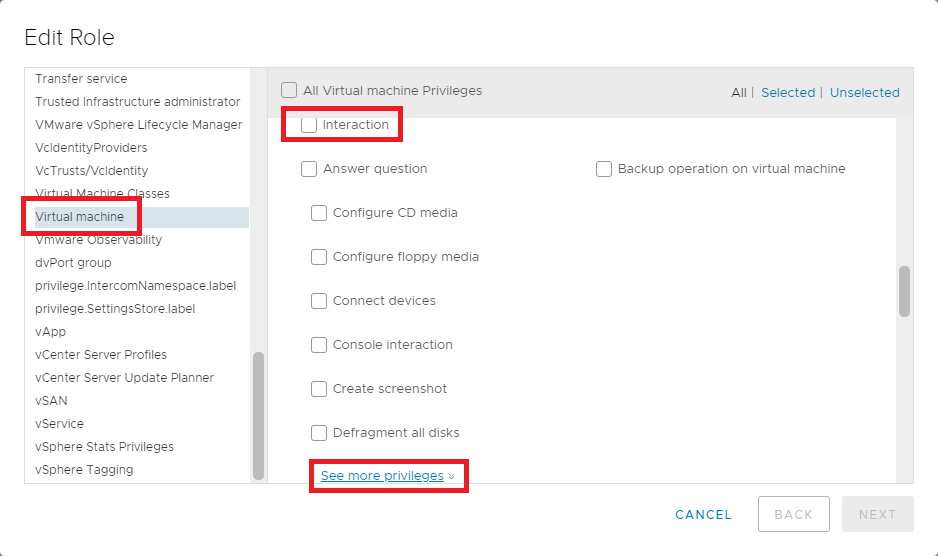
In the left pane, scroll down to Virtual machine, and in the right pane, scroll down to Interaction, and click See more privileges, as shown in Figure 16.
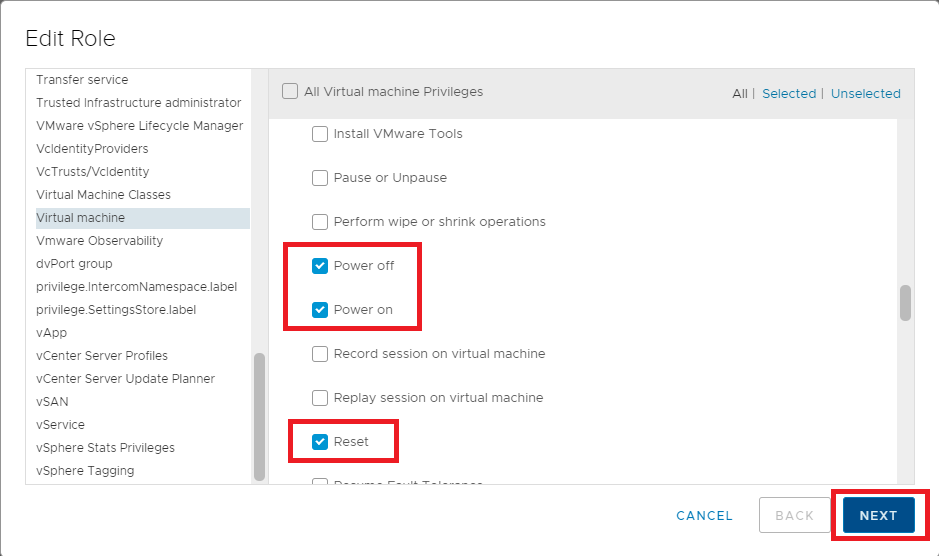
In the right pane, scroll down and select Power off, Power on, Reset, and click Next, as shown in Figure 17.
Click Finish, as shown in Figure 18.
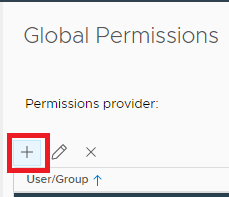
In Global Permissions, click the “+“, as shown in Figure 19.
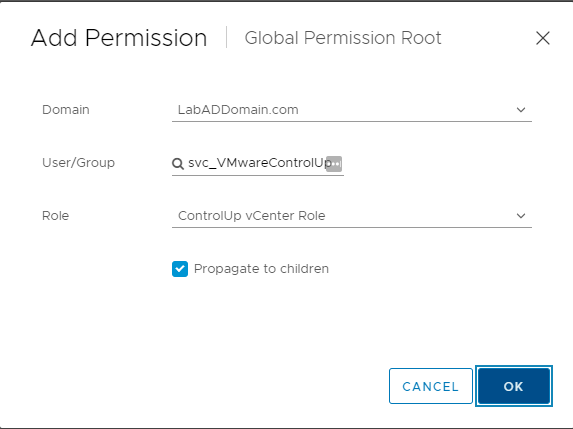
Change the Domain to the AD domain, select the new ControlUp AD service account for User/Group, select the Custom Role, select Propagate to children, and click OK, as shown in Figure 20.
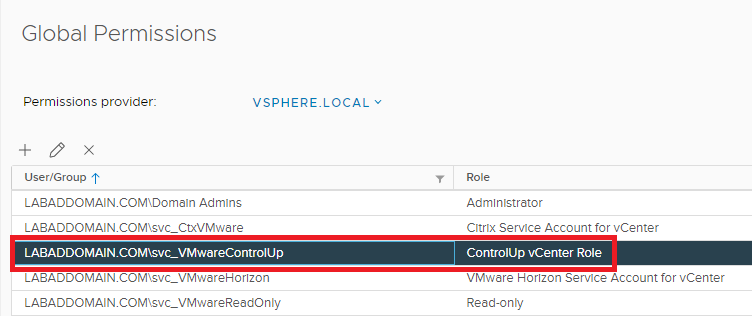
The new ControlUp account is added to the list, as shown in Figure 21.
Additional XenCenter Configuration
The XenCenter Read-Only role created earlier is sufficient for all monitoring purposes. However, we want to use the built-in hypervisor-based VM power management functions. Therefore, we need to create a custom role based on the Read-Only role, adding the VM Operators permission.
Start and, if required, connect or log in to XenCenter.
First, we need to create an AD service account to assign the XenCenter Custom Role.
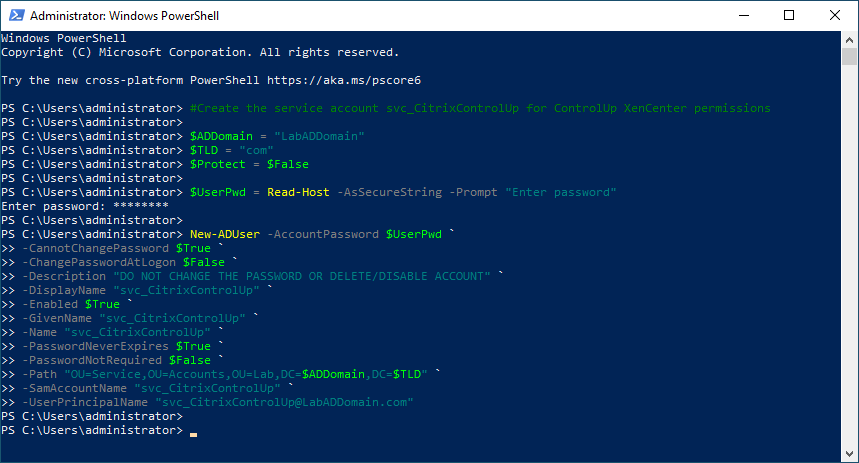
From the Lab’s management computer, start an elevated PowerShell session, copy and paste the following into the elevated PowerShell session, and press Enter, as shown in Figure 22.
Remember to set the values you need.
Note: Lines may wrap
#Create the service account svc_CitrixControlUp for ControlUp XenCenter permissions $ADDomain = "LabADDomain" $TLD = "com" $Protect = $False $UserPwd = Read-Host -AsSecureString -Prompt "Enter password" New-ADUser -AccountPassword $UserPwd ` -CannotChangePassword $True ` -ChangePasswordAtLogon $False ` -Description "DO NOT CHANGE THE PASSWORD OR DELETE/DISABLE ACCOUNT" ` -DisplayName "svc_CitrixControlUp" ` -Enabled $True ` -GivenName "svc_CitrixControlUp" ` -Name "svc_CitrixControlUp" ` -PasswordNeverExpires $True ` -PasswordNotRequired $False ` -Path "OU=Service,OU=Accounts,OU=Lab,DC=$ADDomain,DC=$TLD" ` -SamAccountName "svc_CitrixControlUp" ` -UserPrincipalName "[email protected]"
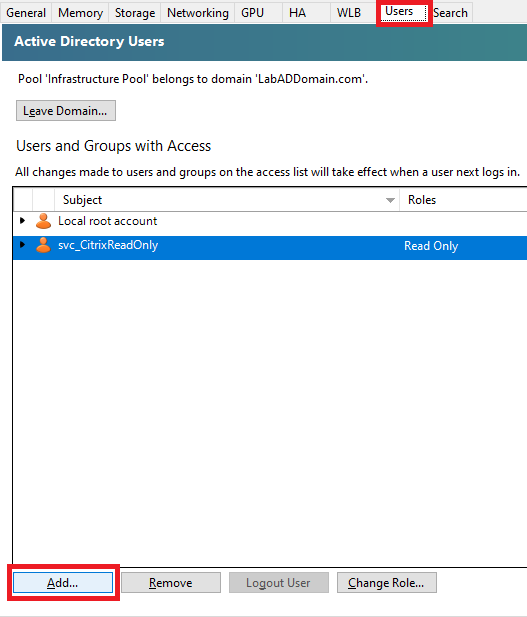
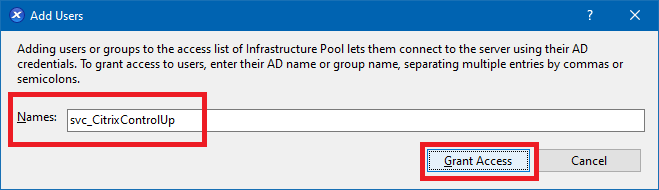
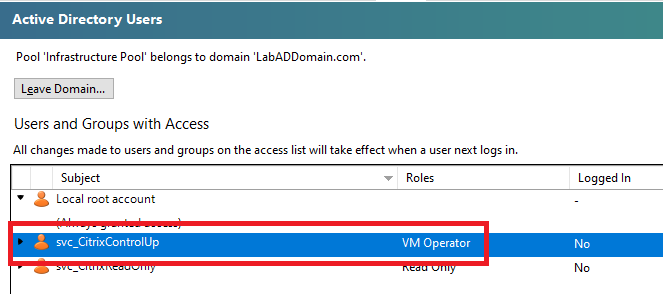
In XenCenter, click the Resource Pool and in the right pane, click Users, click Add…, as shown in Figure 23.
Enter the name of the new Citrix ControlUp account and click Grant Access, as shown in Figure 24.
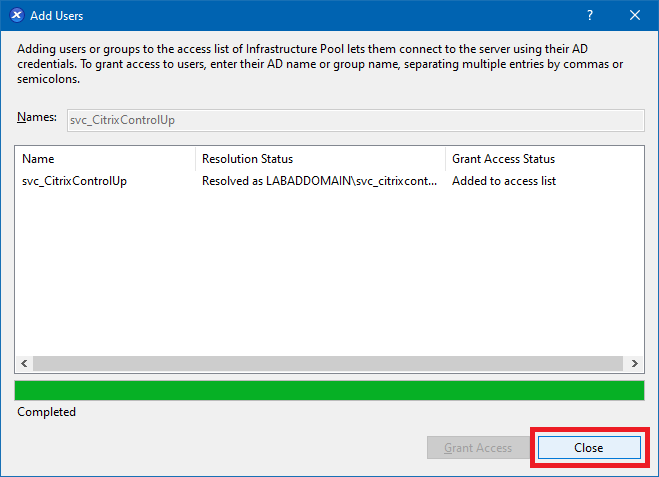
Click Close, as shown in Figure 25.
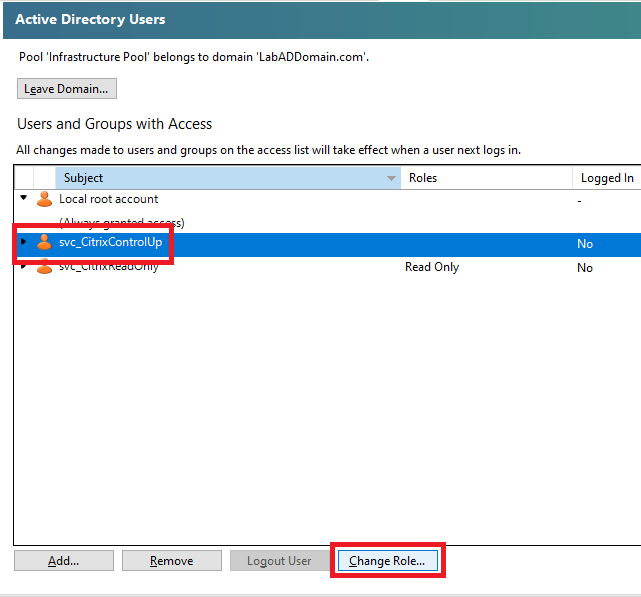
Select the Citrix ControlUp account and click Change Role…, as shown in Figure 26.
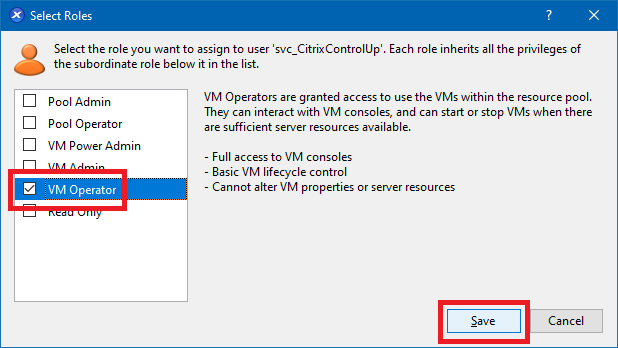
Select VM Operator and click Save, as shown in Figure 27.
The account is ready for use, as shown in Figure 28.
GPOs
Before installing and configuring ControlUp, we need four GPOs created.
- One for the ControlUp server Windows Defender exclusions
- One for the ControlUp server Windows Firewall ports
- One for the monitored computers Windows Defender exclusions
- One for the monitored computers Windows Firewall ports
On the Lab management computer, open the Group Policy Management Console (GPMC).
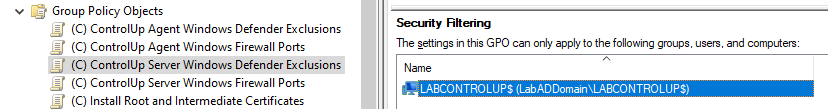
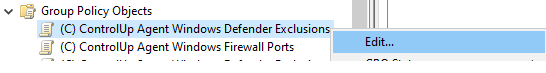
In the Group Policy Objects node, create and name four GPOs. For example, I named mine as follows:
- (C) ControlUp Agent Windows Defender Exclusions – linked at the domain level, Deny applied to LabControlUp
- (C) ControlUp Agent Windows Firewall Ports – linked at the domain level, Deny applied to LabControlUp
- (C) ControlUp Server Windows Defender Exclusions – linked to the ControlUp OU and applied only to the LabControlUp computer account
- (C) ControlUp Server Windows Firewall Ports – linked to the ControlUp OU and applied only to the LabControlUp computer account
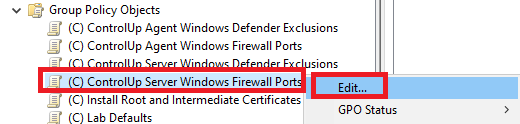
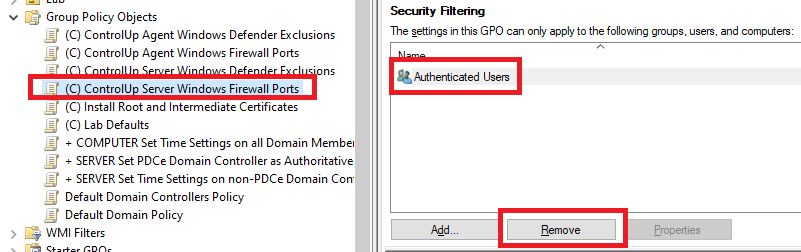
Let’s work on the (C) ControlUp Server Windows Firewall Ports GPO first.
We need the following Windows Firewall ports configured for the server.
ControlUp Server
- TCP 53 open outbound for name resolution
- TCP 80 open outbound for communication to XenServer, XenDesktop, and NetScalers/ADCs
- TCP 135 – 139, 445, and 49152 – 65535 for Agent deployment and upgrades via the console and specific OOB actions, such as restarting the agent.
- TCP 389 open outbound for LDAP communication with domain controllers
- TCP 443 opened outbound for communication to vSphere, Horizon, ControlUp Cloud servers, and NetScalers/ADCs
- TCP 40705 open outbound for Console to agent communication via the WCF protocol.
- TCP 40706 open outbound for Console to Monitor management port.
A summary of these ports is 53, 80, 135 – 139, 389, 443, 445, 40705, 40706, 49152 – 65535.
In the GPMC, right-click the (C) ControlUp Server Windows Firewall Ports GPO in the Group Policy Object node and click Edit, as shown in Figure 29.
Expand Policies.
Expand Windows Settings.
Expand Security Settings.
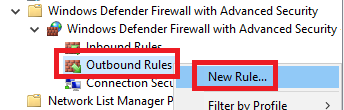
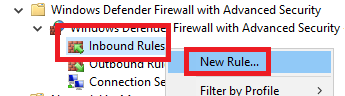
Expand Windows Defender Firewall with Advanced Security.
Expand Windows Defender Firewall with Advanced Security.
Right-click Outbound Rules and click New Rule…, as shown in Figure 30.
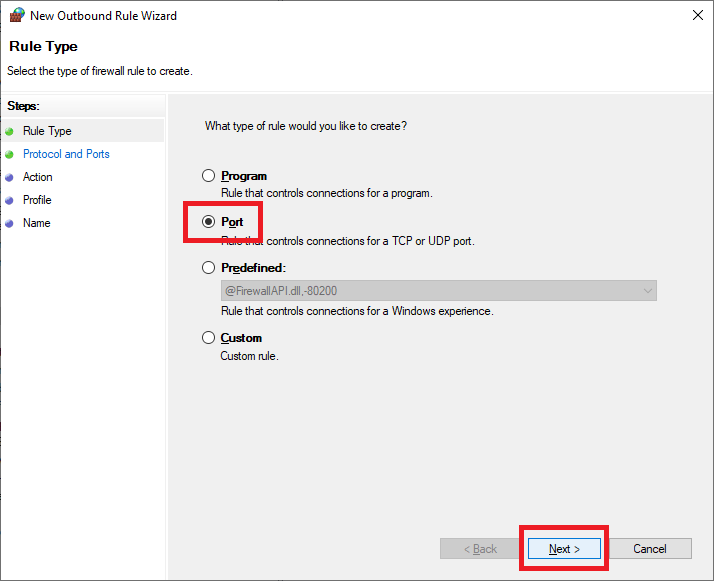
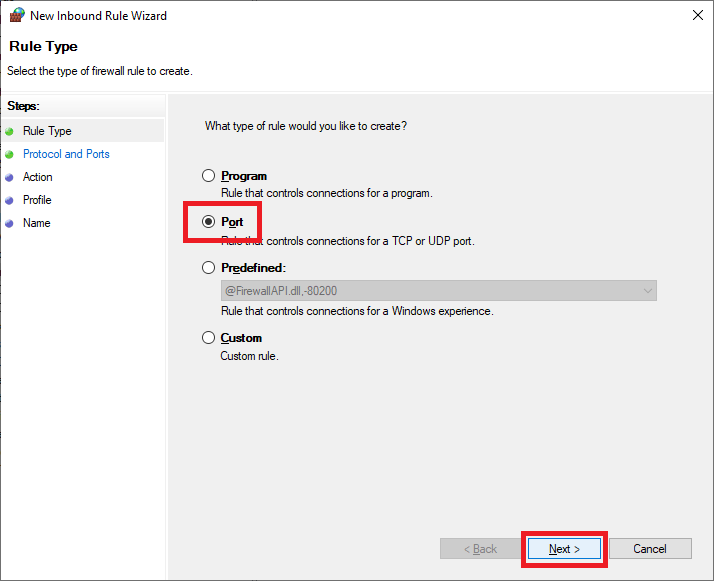
Select Port and click Next, as shown in Figure 31.
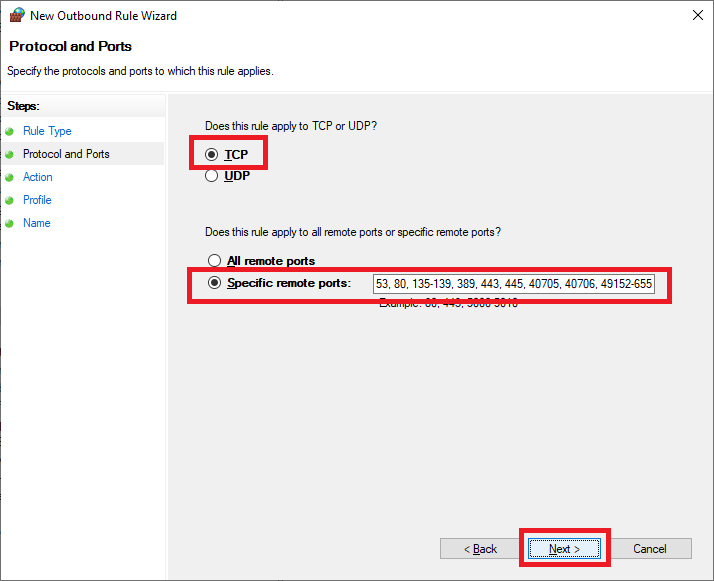
Select TCP, select Specific local ports, enter 53, 80, 135-139, 389, 443, 445, 40705, 40706, 49152-65535, and click Next, as shown in Figure 32.
Note: There are no spaces before or after the dash in “135-139” and “49152-65535”. If you get an error message in the GPME about invalid characters, verify that the dash character (“-“) is not a copy and paste error from your browser and there are no spaces.
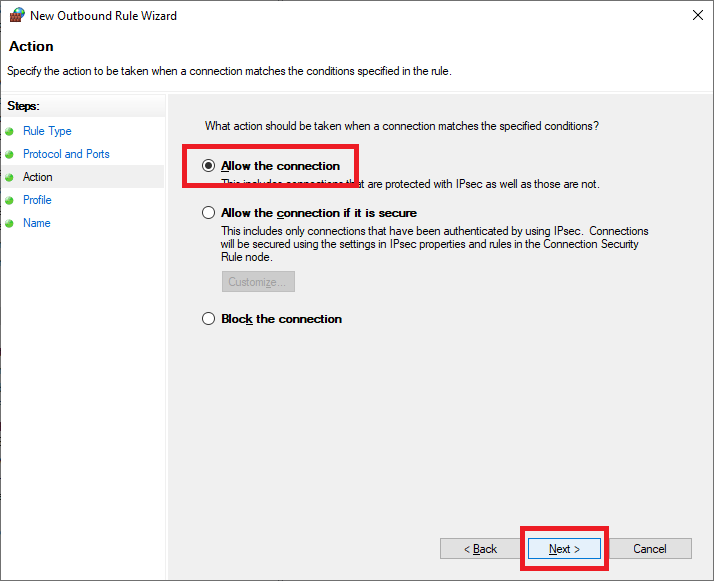
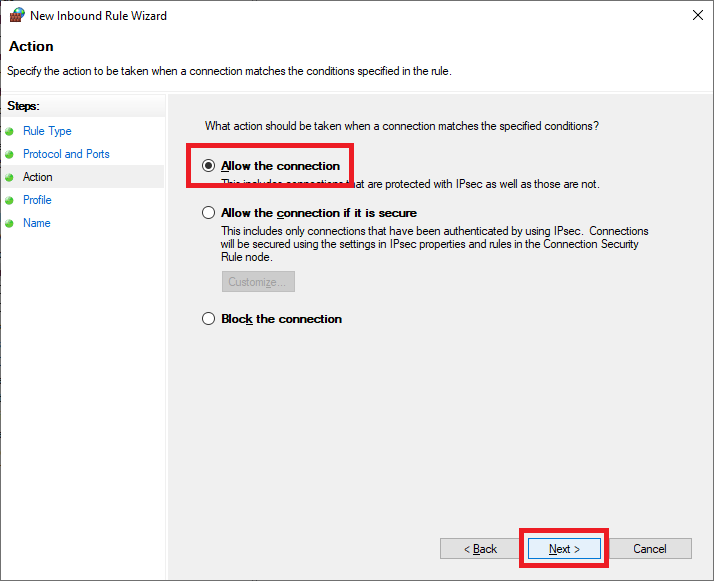
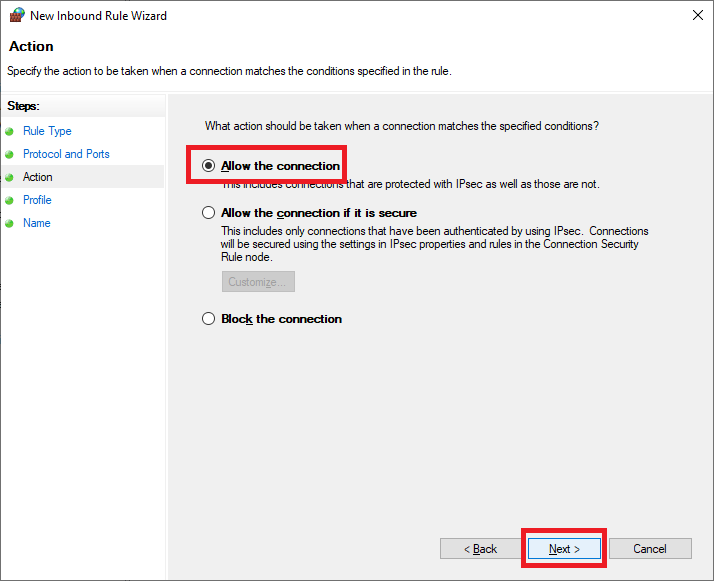
Select Allow the connection and click Next, as shown in Figure 33.
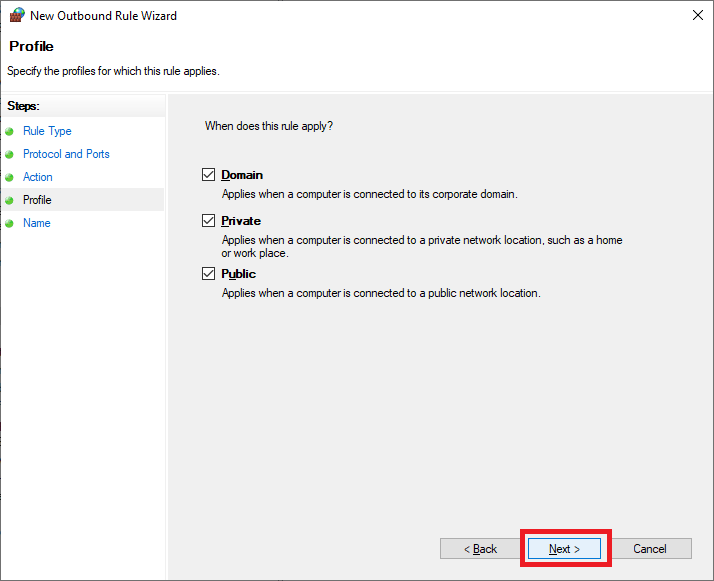
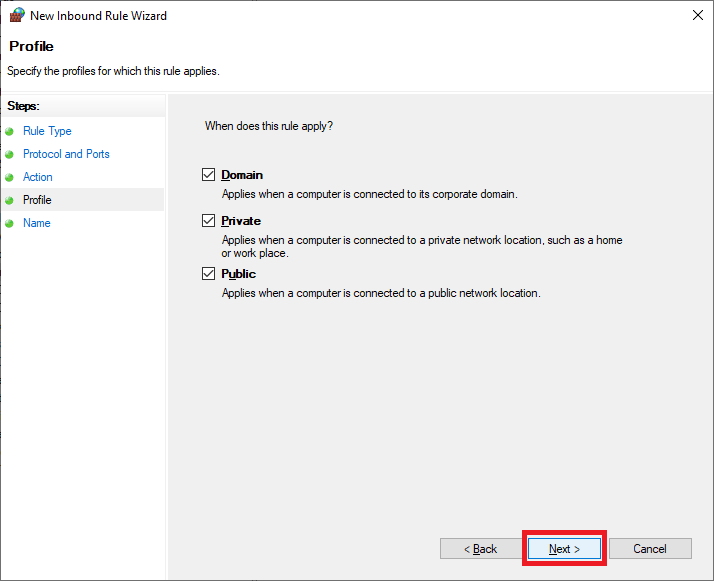
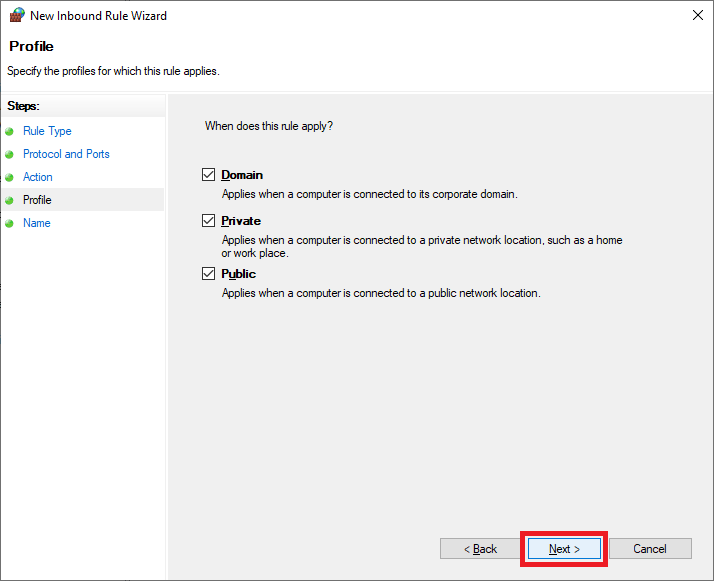
Click Next, as shown in Figure 34.
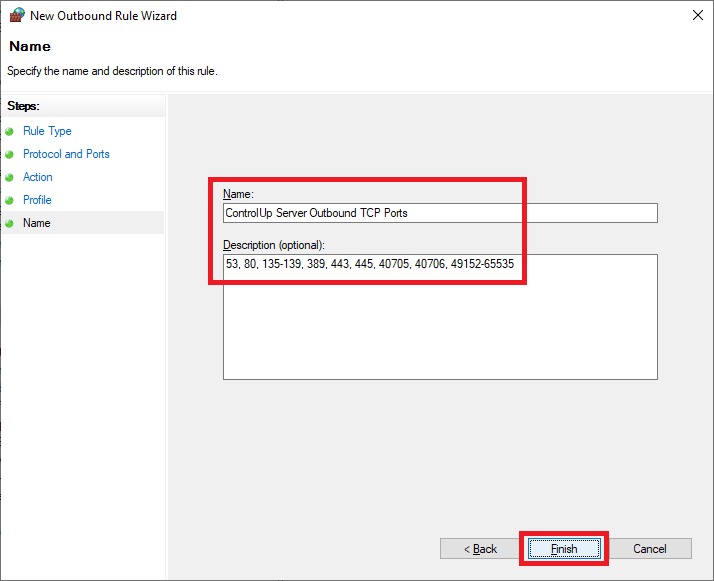
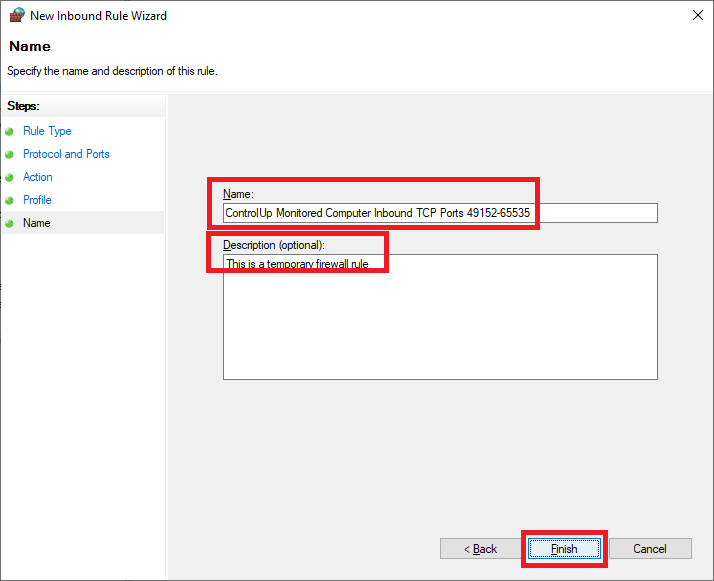
Enter a Name, an optional Description, and click Finish, as shown in Figure 35.
Exit the Group Policy Management Editor (GPME).
This GPO applies only to the ControlUp server.
In the middle pane, in Security Filtering, click on Authenticated Users and click Remove, as shown in Figure 36.
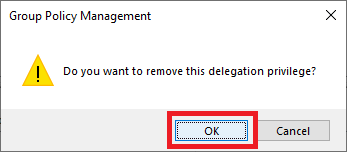
Click OK, as shown in Figure 37.
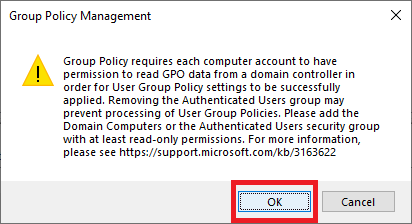
Click OK, as shown in Figure 38.
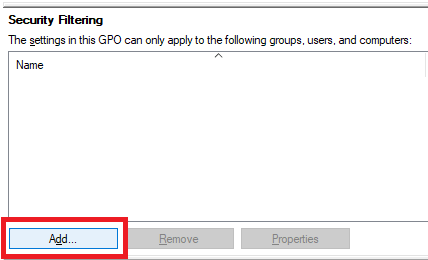
Click Add, as shown in Figure 39.
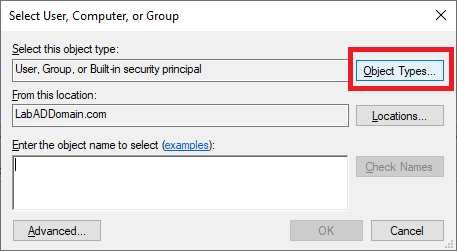
Click Object Types…, as shown in Figure 40.
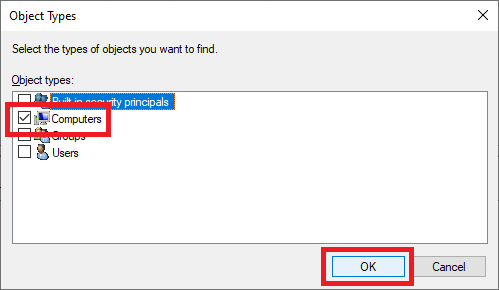
Select only Computers and click OK, as shown in Figure 41.
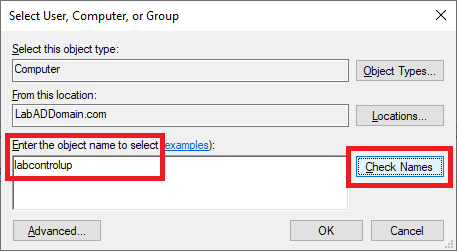
Type in the name of the ControlUp server and click Check Names, as shown in Figure 42.
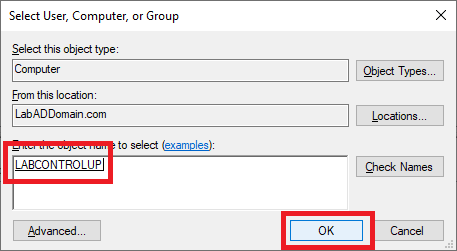
Once the computer name is verified, click OK, as shown in Figure 43.
Now onto the (C) ControlUp Server Windows Defender Exclusions GPO.
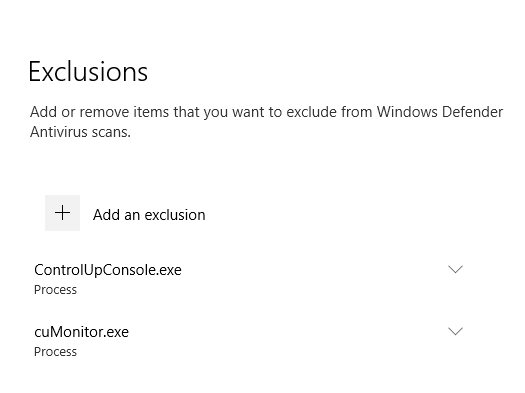
Here are the exclusions needed for the ControlUp server.
- ControlUp Server
- Process Exclusions:
- ControlUpConsole.exe
- cuMonitor.exe
- Process Exclusions:
Right-click the (C) ControlUp Server Windows Defender Exclusions GPO in the left pane and click Edit.
Expand Policies.
Expand Administrative Templates.
Expand Windows Components.
Expand Windows Defender Antivirus.
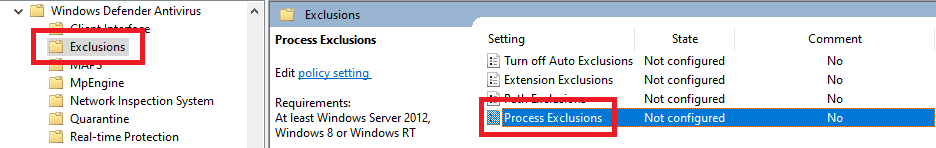
Click on Exclusions.
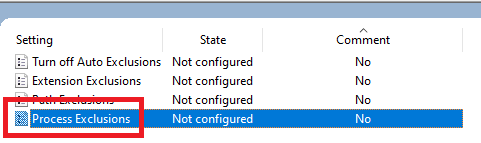
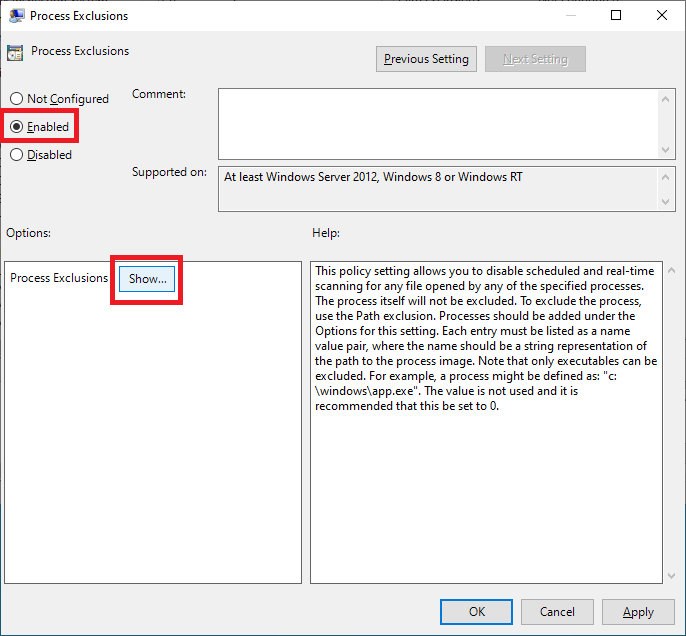
Double-click Process Exclusions, as shown in Figure 44.
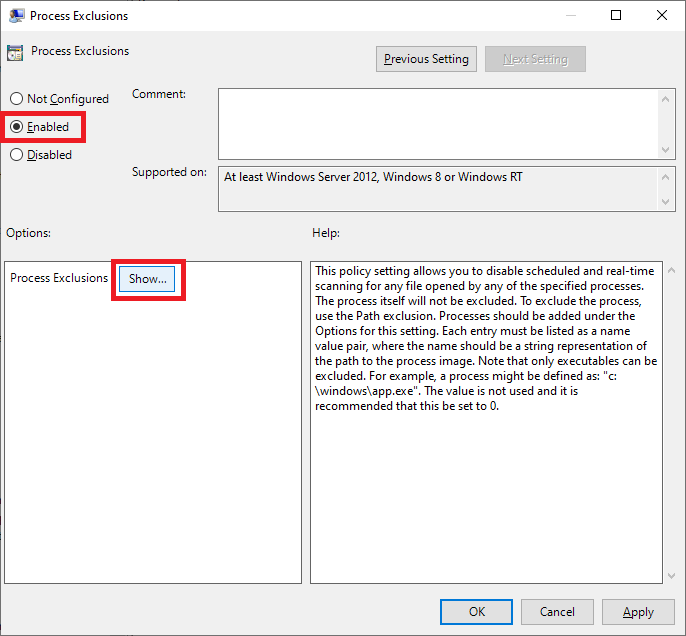
Select Enabled and click Show…, as shown in Figure 45.
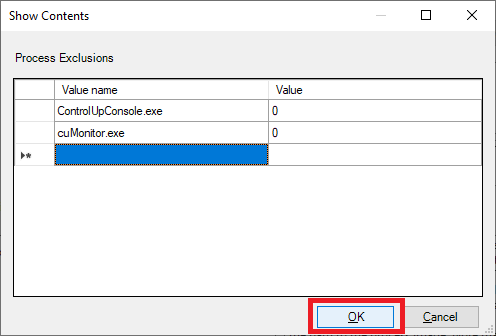
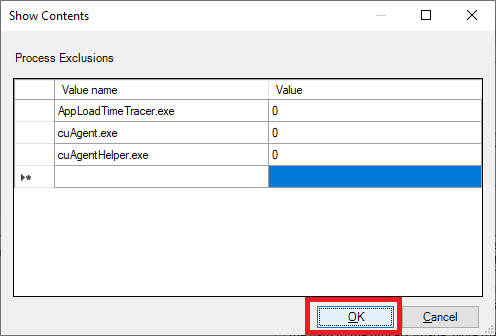
Enter the values shown in Figure 46, and click OK.
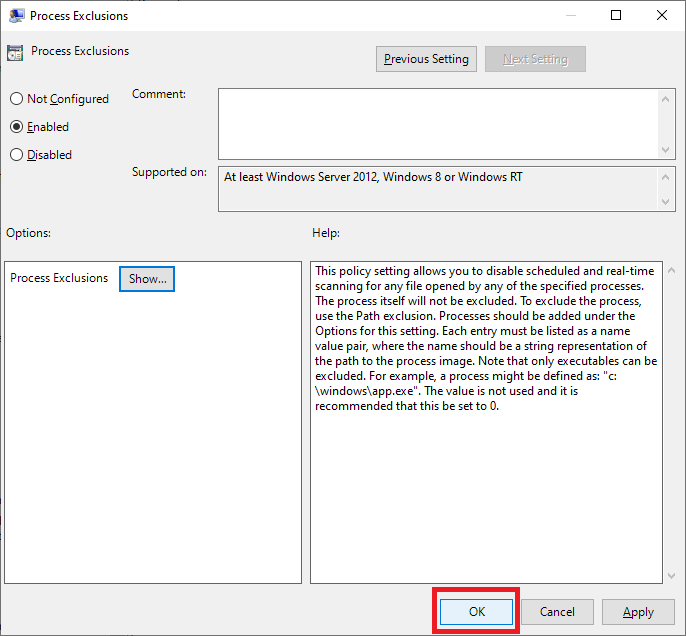
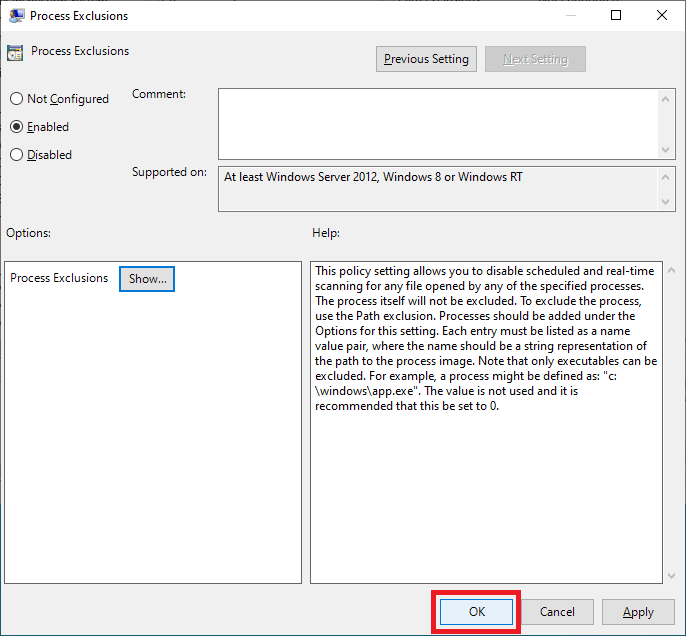
Click OK, as shown in Figure 47.
Exit the GPME.
Follow the same process as shown in Figures 36 through 43 to remove Authenticated Users and add the ControlUp server, as shown in Figure 48.
Scroll to the top in the GPMC.
Expand Domains.
Expand your AD domain.
Expand the Lab OU.
Expand the Infrastructure OU.
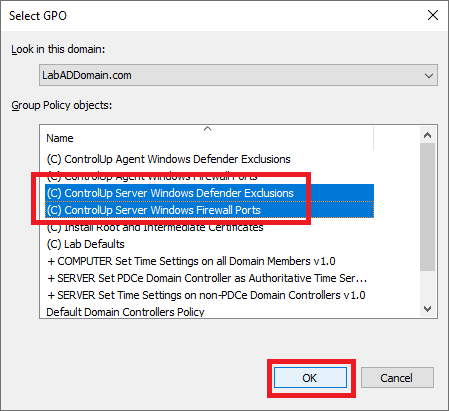
Right-click the ControlUp OU and click Link an Existing GPO…, as shown in Figure 49.
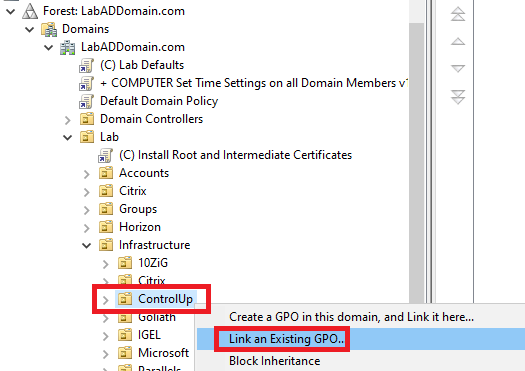
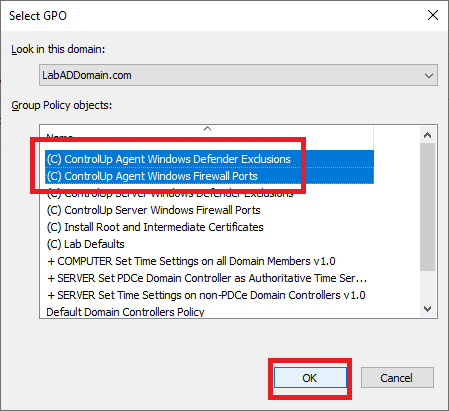
Select both ControlUp server GPOs and click OK, as shown in Figure 50.
Now that we have the two ControlUp server GPOs created let’s move on to the GPOs for the monitored computers.
Let’s work on the (C) ControlUp Agent Windows Firewall Ports GPO first.
We need the following Windows Firewall ports configured for the monitored computers.
ControlUp Agent
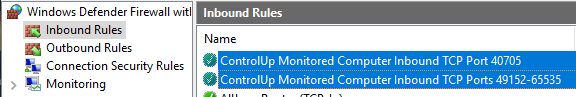
- TCP 40705 open inbound for ongoing console/monitor communications. This is a permanent rule.
- TCP 49152 – 65535 for Agent deployment and upgrades via the console and specific OOB actions, such as restarting the agent. We need these ports temporarily for deploying the agent.
In the GPMC, right-click the (C) ControlUp Agent Windows Firewall Ports GPO in the Group Policy Object node and click Edit.
Expand Policies.
Expand Windows Settings.
Expand Security Settings.
Expand Windows Defender Firewall with Advanced Security.
Expand Windows Defender Firewall with Advanced Security.
First, we create the permanent rule for TCP port 40705.
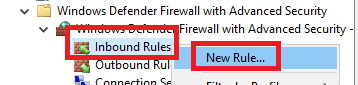
Right-click Inbound Rules and click New Rule…, as shown in Figure 51.
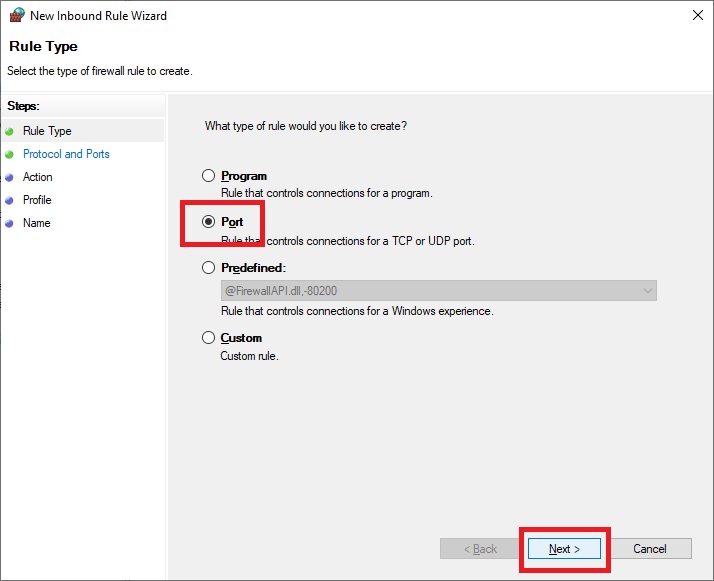
Select Port and click Next, as shown in Figure 52.
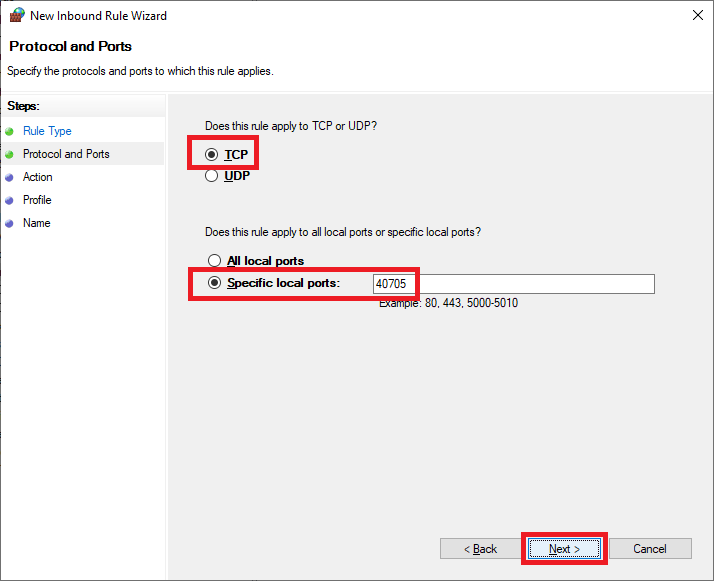
Select TCP, select Specific local ports, enter 40705, and click Next, as shown in Figure 53.
Select Allow the connection and click Next, as shown in Figure 54.
Click Next, as shown in Figure 55.
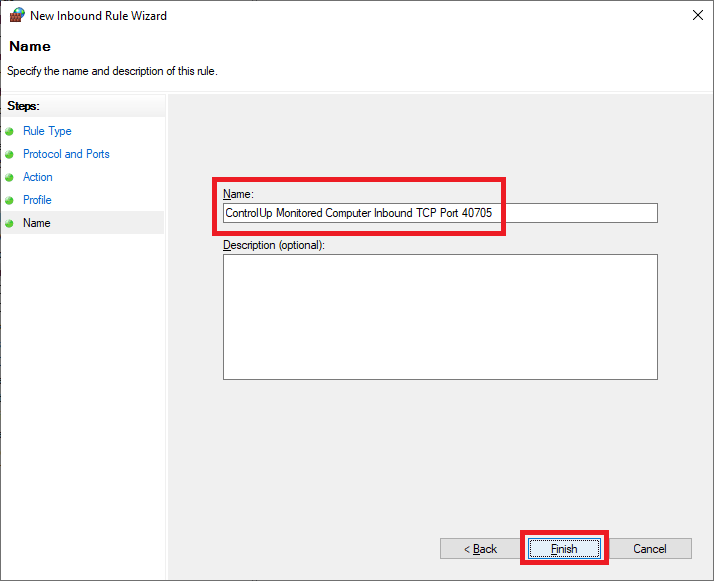
Enter a Name, an optional Description, and click Next, as shown in Figure 56.
Next, we have to create the temporary rule for TCP ports 49152-65535 (the high RPC ports).
Right-click Inbound Rules and click New Rule…, as shown in Figure 57.
Select Port and click Next, as shown in Figure 58.
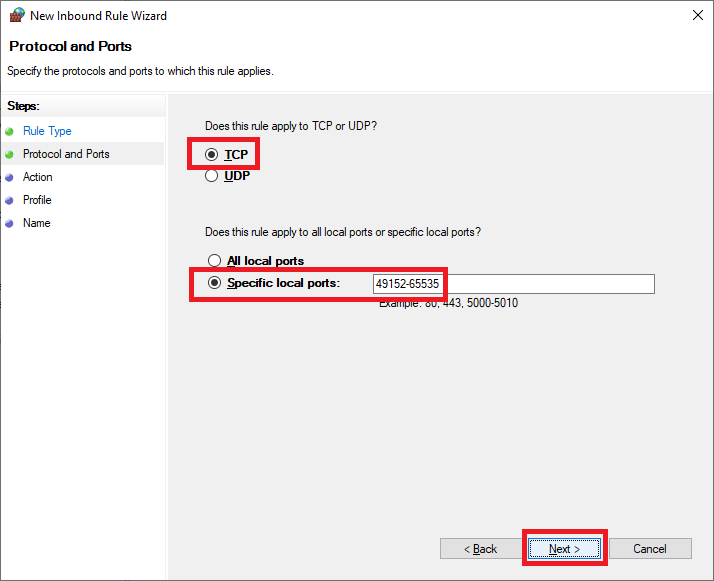
Select TCP, select Specific local ports, enter 49152-65535, and click Next, as shown in Figure 59.
Note: There are no spaces before or after the dash in “49152-65535”. If you get an error message in the GPME about invalid characters, verify that the dash character (“-“) is not a copy and paste error from your browser and there are no spaces.
Select Allow the connection and click Next, as shown in Figure 60.
Click Next, as shown in Figure 61.
Enter a Name, an optional Description, and click Next, as shown in Figure 62.
Exit the Group Policy Management Editor (GPME).
This GPO applies to the computers monitored by the ControlUp server.
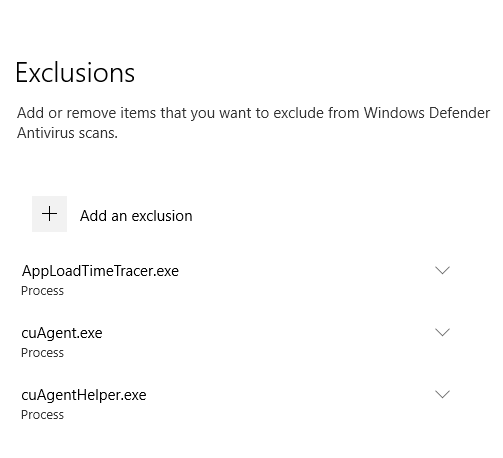
Now onto the (C) ControlUp Agent Windows Defender Exclusions GPO.
Here are the exclusions needed for the monitored computers.
- VMs/Servers with Agents on them (For example, Citrix machines, VMware Horizon machines, VMs.)
- Process Exclusions:
- AppLoadTimeTracer.exe
- cuAgentexe
- cuAgentHelper.exe
- Process Exclusions:
In the left pane, right-click the (C) ControlUp Agent Windows Defender Exclusions GPO and click Edit.
Expand Policies.
Expand Administrative Templates.
Expand Windows Components.
Expand Windows Defender Antivirus.
In the left pane, click on Exclusions, and in the middle pane, double-click Process Exclusions, as shown in Figure 63.
Select Enabled and click Show…, as shown in Figure 64.
Enter the values shown in Figure 65, and click OK.
Click OK, as shown in Figure 66.
Exit the GPME.
Collapse the Lab OU.
These two GPOs do not apply to the ControlUp server. To do that, we configure a GPO Deny Policy. A Deny right is not something you should do as a normal course of working with GPOs as it complicates GPO troubleshooting.
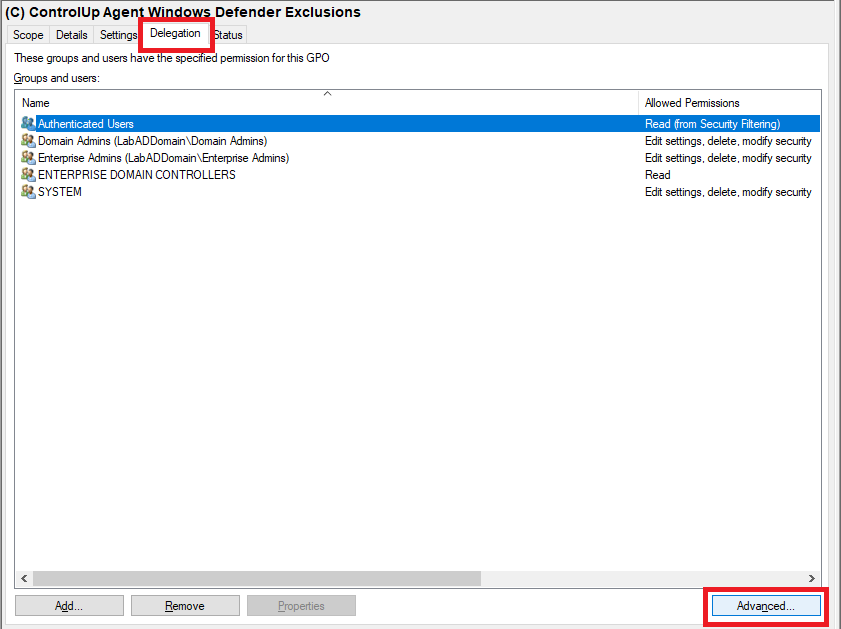
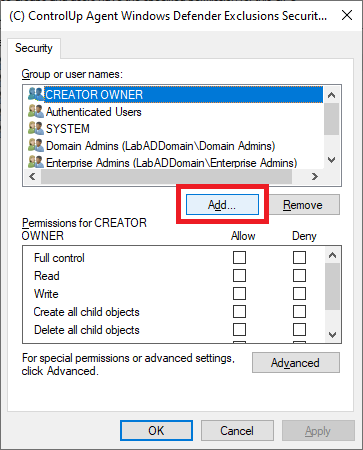
Click on the (C) ControlUp Agent Windows Defender Exclusions GPO, and in the middle pane, click the Delegation tab and click Advanced, as shown in Figure 67.
Click Add…, as shown in Figure 68.
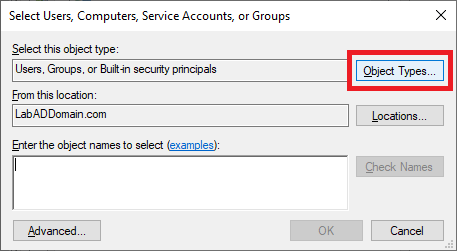
Click on Object Types…, as shown in Figure 69.
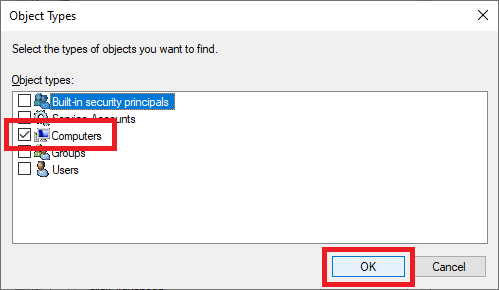
Select only Computers and click OK, as shown in Figure 70.
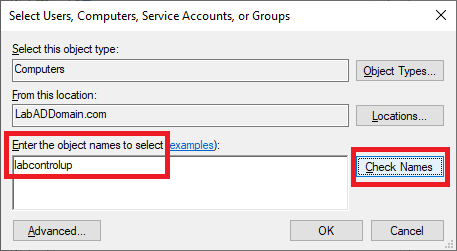
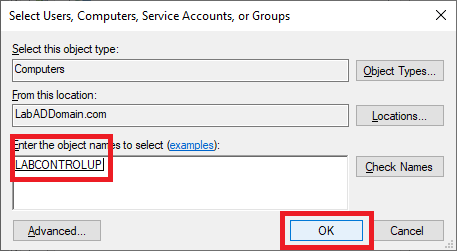
Type in the name of the ControlUp server and click Check Names, as shown in Figure 71.
When the server name is validated, click OK, as shown in Figure 72.
Verify that the ControlUp server is selected, and in the Permissions area, scroll down and select Deny for Apply group policy, as shown in Figure 73. Do NOT change any other permissions.
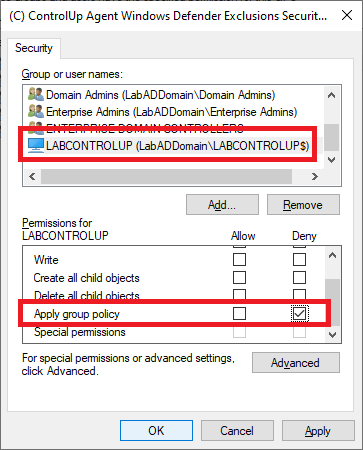
Click Yes, as shown in Figure 74.
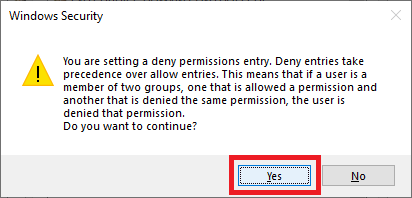
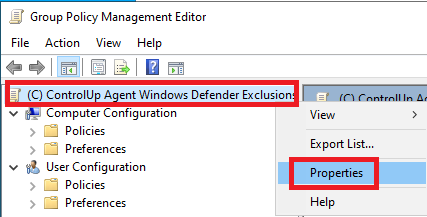
Right-click the GPO and click Edit, as shown in Figure 75.
Right-click the top level of the GPO and click Properties, as shown in Figure 76.
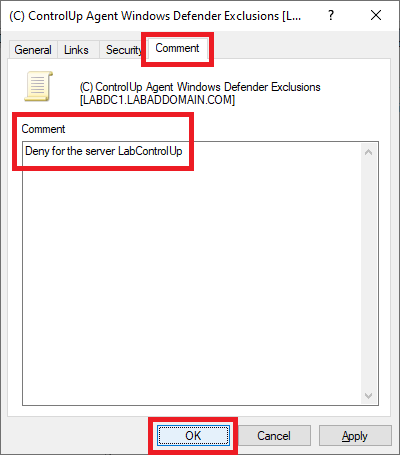
Click the Comment tab. For the comment, type in Deny for the server <ControlUp server name>, and click OK, as shown in Figure 77. This comment makes it easier when troubleshooting the GPO later.
Exit the GPME.
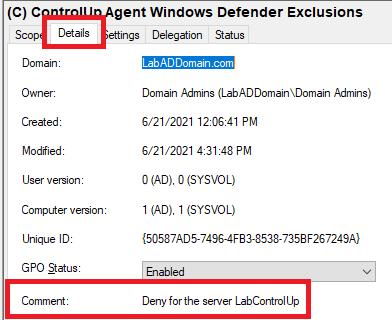
Figure 78 shows the comment entered.
Repeat the process to add the Deny permission to the other GPO.
Scroll to the top in the GPMC.
Expand Domains.
Expand your AD domain.
Right-click the domain and click Link an Existing GPO…, as shown in Figure 79.
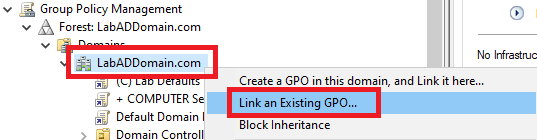
Select both ControlUp agent monitoring GPOs and click OK, as shown in Figure 80.
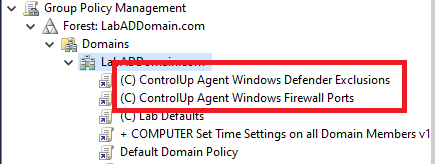
The two GPOs are now linked at the domain level, as shown in Figure 81.
To verify the GPOs work, log in to the file server and the ControlUp server.
Tip: If the GPOs do not work at first, either restart the VM or do a Right-click Start, Run, gpupdate. Then log off and back on to see if it took effect. Gpupdate is a command-line utility from Microsoft that comes with all versions of the Windows operating system to refresh the Group Policy engine on the client. There are many ways of running gpupdate. As an administrator, you can even force a group policy refresh remotely using PowerShell or the GPMC.
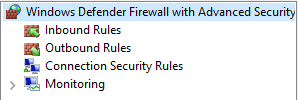
On the ControlUp server, right-click Start, Run, wf.msc, and Windows Defender Firewall with Advanced Security starts, as shown in Figure 82.
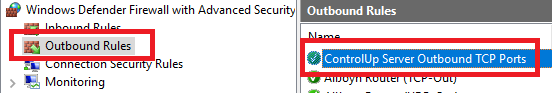
Click Outbound Rules and verify that the Outbound Firewall Rule configured by the GPO is there, as shown in Figure 83.
Exit Windows Defender Firewall with Advanced Security.
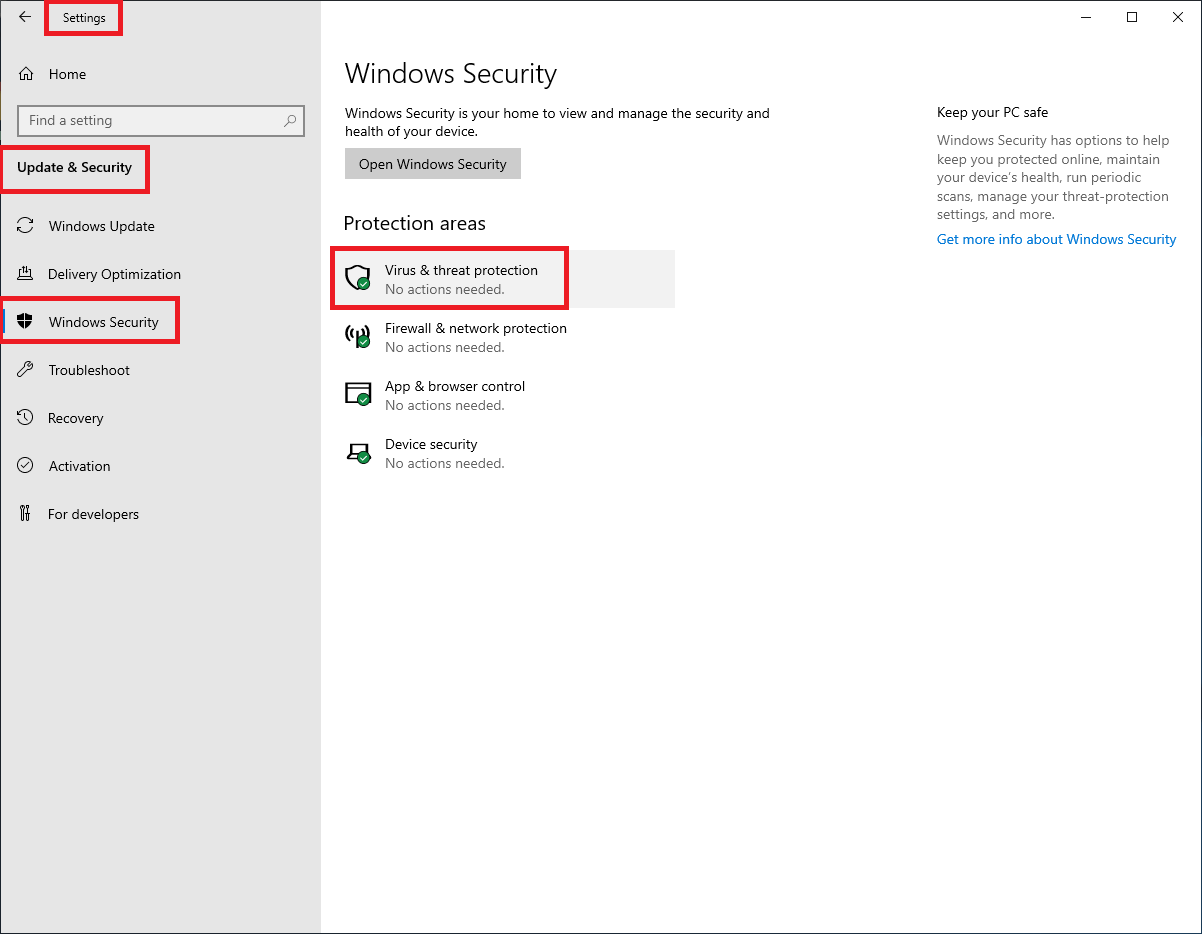
To verify the Windows Defender Exclusions, click Start, Settings, Update & Security, Windows Security, and Virus & threat protection, as shown in Figure 84.
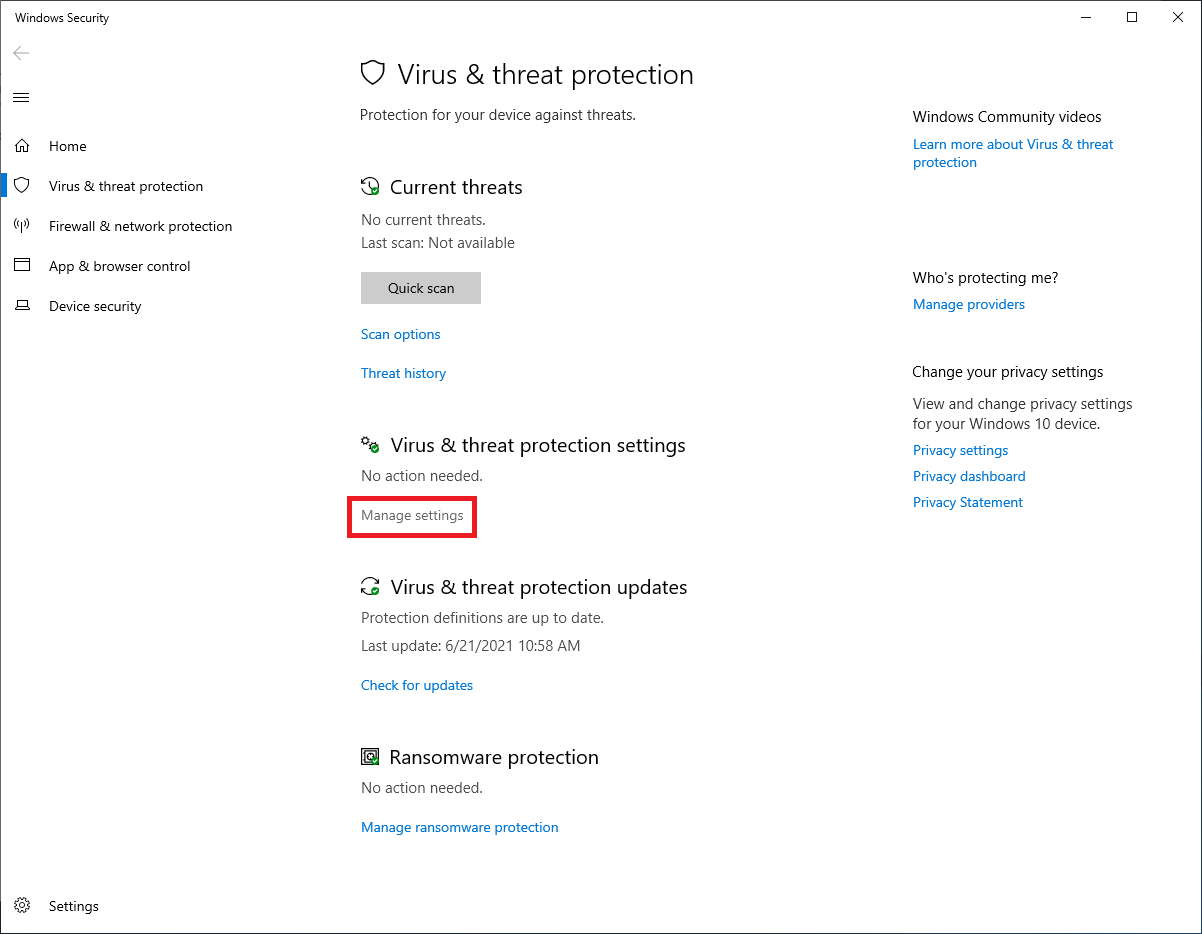
Under Virus & threat protection settings, click Manage settings, as shown in Figure 85.
Scroll down to Exclusions and click Add or remove exclusions, as shown in Figure 86.
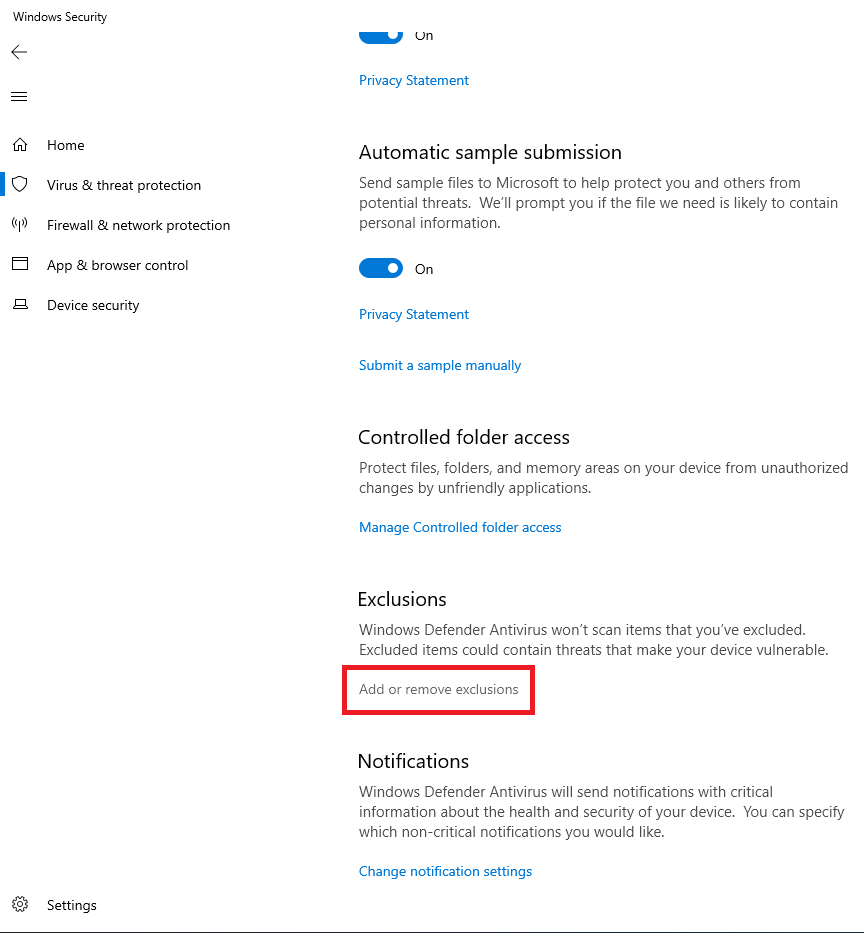
Figure 87 shows that the Exclusions are in place.
Follow the same process to validate the GPO settings on the file server, as shown in Figures 88 and 89.
Install ControlUp Performance Monitor
Extract the downloaded ControlUp.zip file to the ControlUp server to C:\ControlUp, as shown in Figure 90.
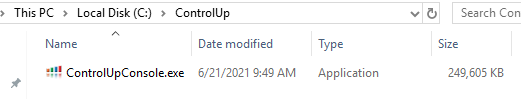
There is nothing to install for ControlUp. ControlUpConsole.exe is the ControlUp monitoring software.
Before continuing, install a modern internet browser. For example, I installed Google Chrome because I could not get the installer for the new Microsoft Edge to work from Internet Explorer 11 (IE11). ControlUp Insights and Solve require a modern browser.
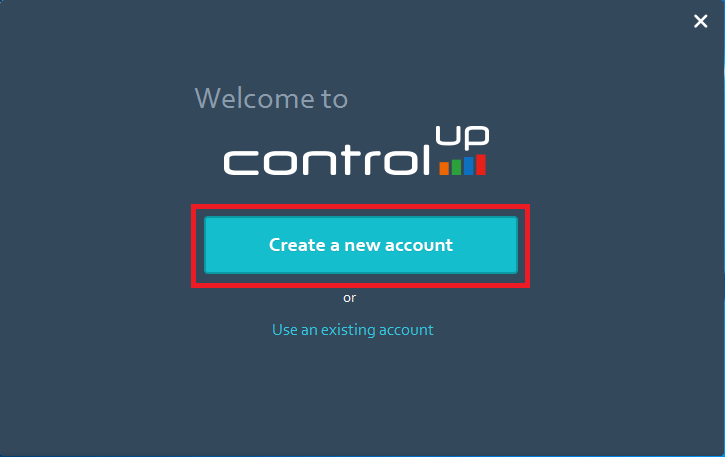
Configuring ControlUp
First Time Launch
Click Create a new account, as shown in Figure 91.
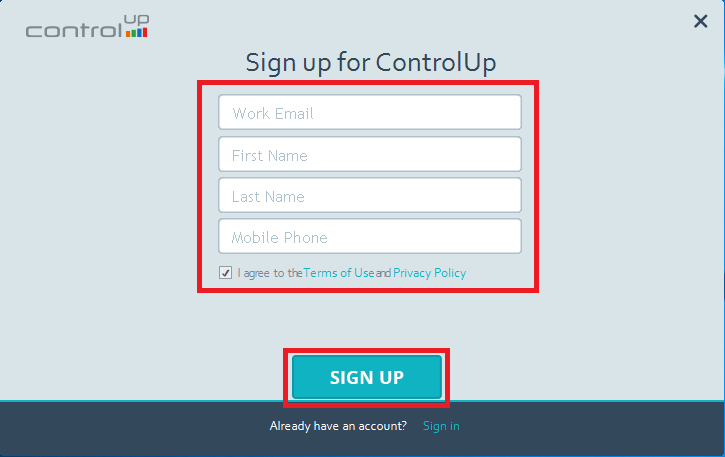
Enter the requested information, select I agree to the Terms of Use and Privacy Policy, and click SIGN UP, as shown in Figure 92.
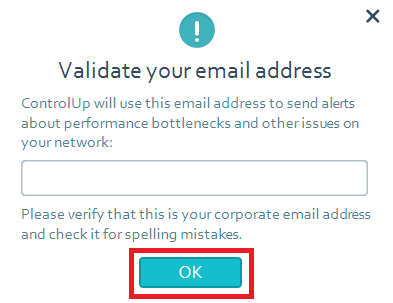
Verify that the email address is correct and click OK, as shown in Figure 93.
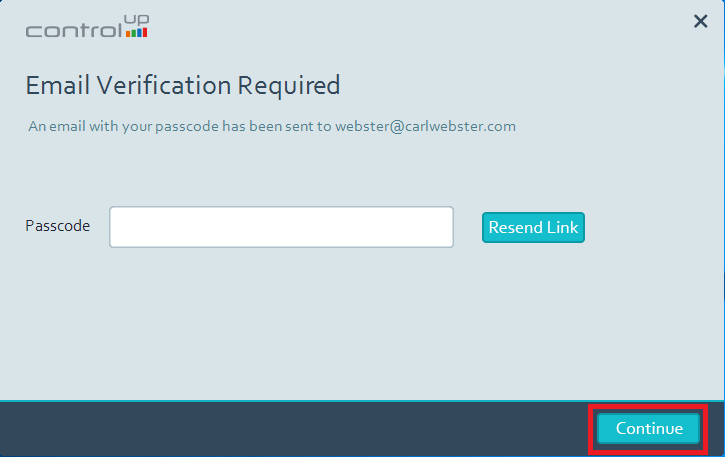
Enter the passcode emailed and click Continue, as shown in Figure 94.
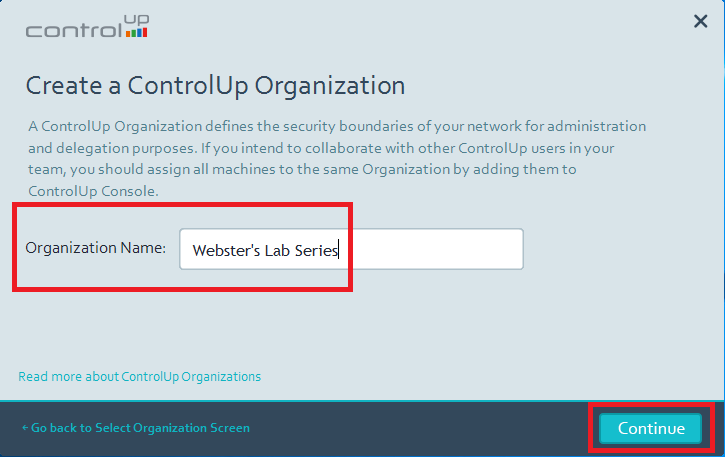
Now you need to create a ControlUp organization. Enter a descriptive Organization Name and click Continue, as shown in Figure 95.
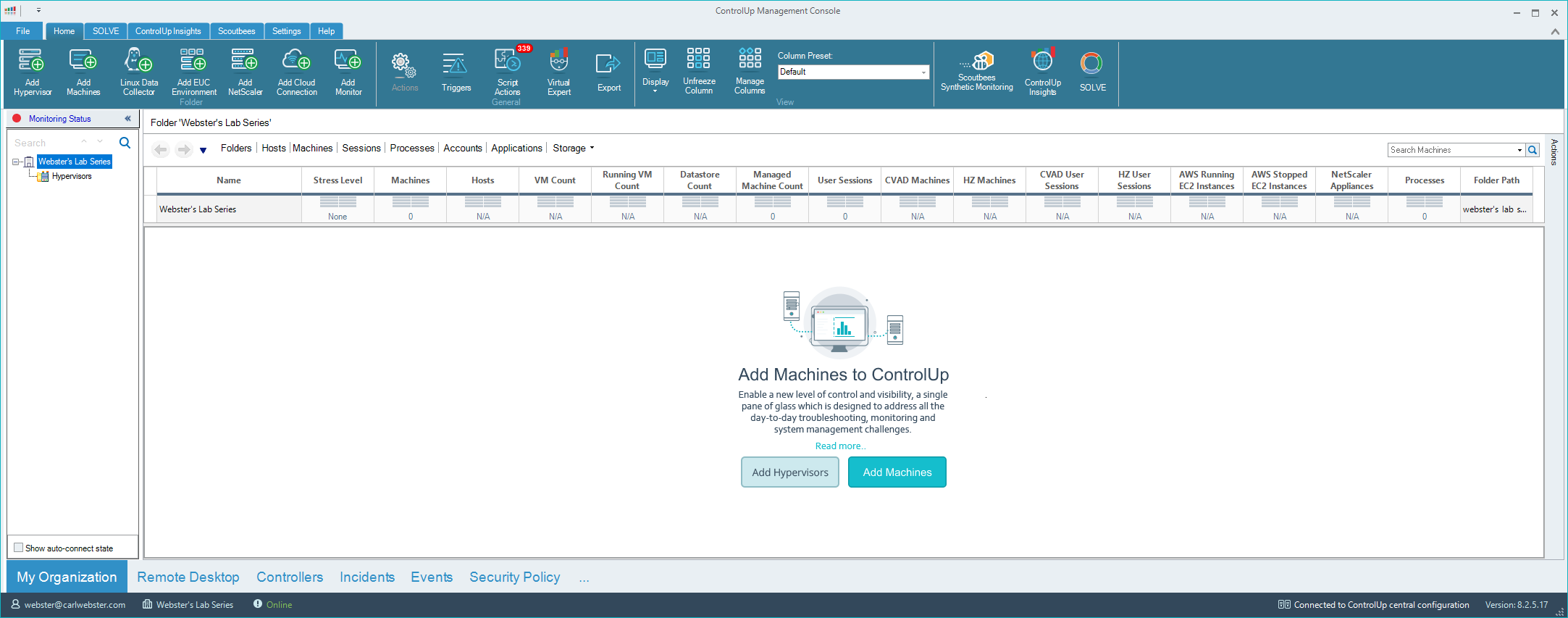
The ControlUp Real-Time Console starts, as shown in Figure 96.
Add Monitor
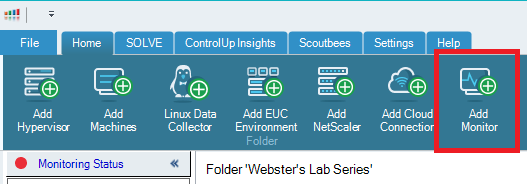
On the toolbar, click Add Monitor, as shown in Figure 97.
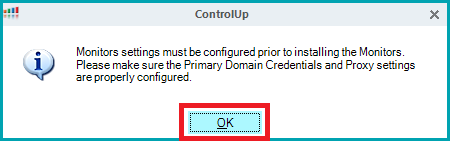
Click OK, as shown in Figure 98.
Click Add Domain, as shown in Figure 99.
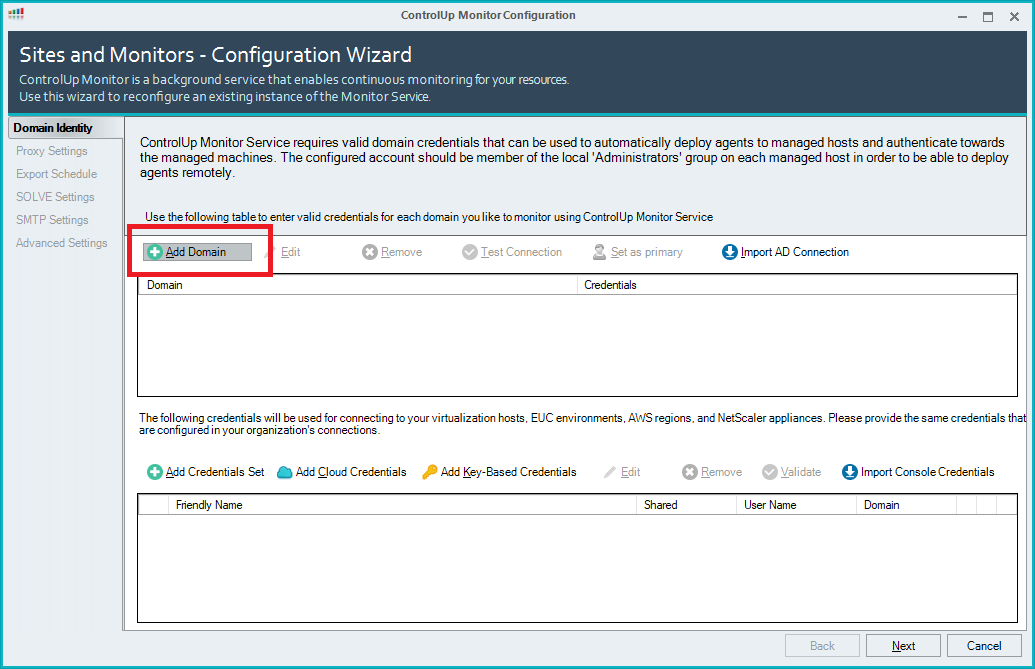
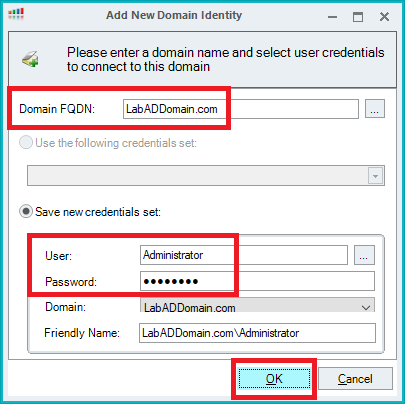
Enter the AD domain’s FQDN, enter domain credentials, and click OK, as shown in Figure 100.
Click Add Credentials Set, as shown in Figure 101.
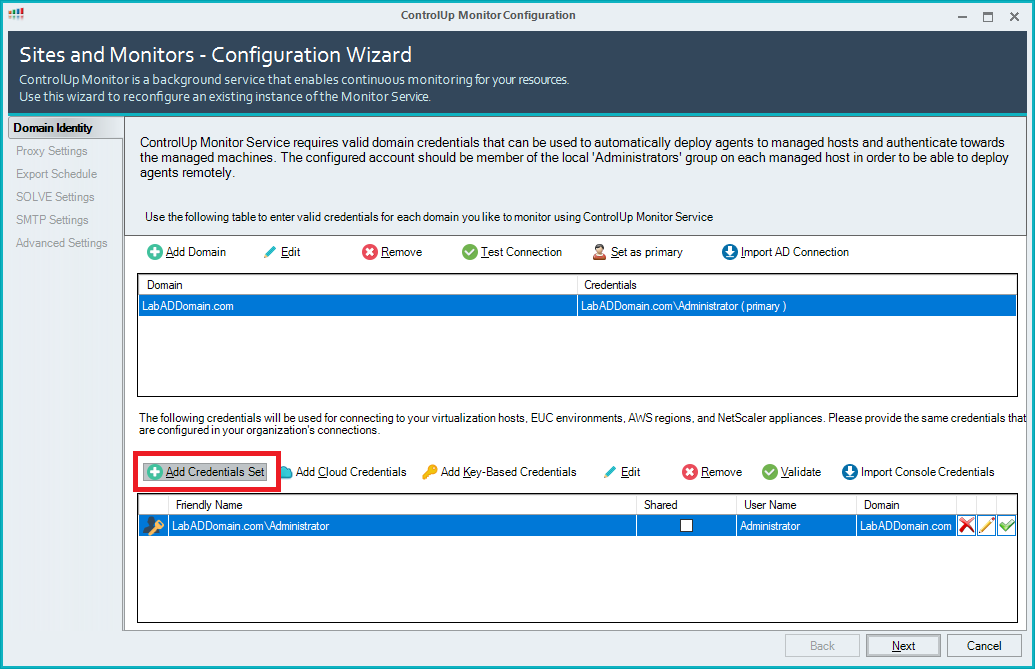
Enter the vCenter ControlUp account information, enter a Friendly Name, select Share credentials with authorized users, and click OK, as shown in Figure 102.
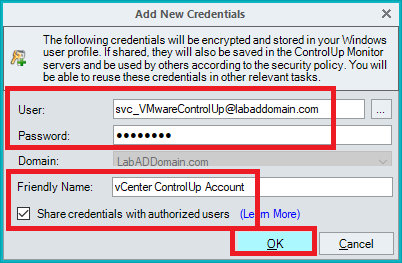
Repeat the process shown in Figures 101 and 102 to add the XenCenter ControlUp account.
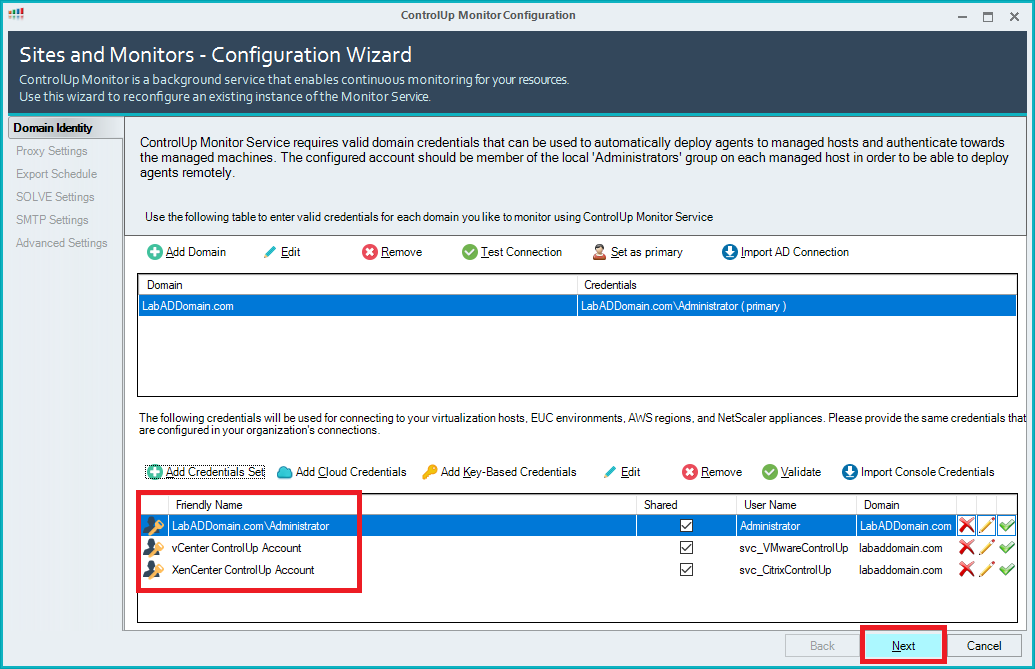
The accounts are added. Click Next, as shown in Figure 103.
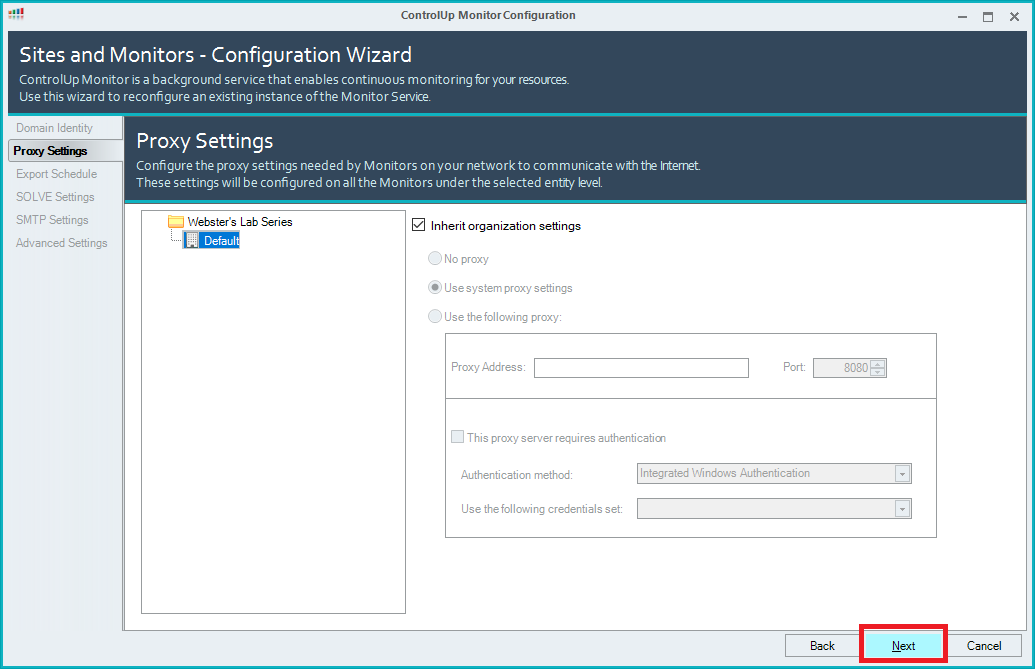
Click Next, as shown in Figure 104.
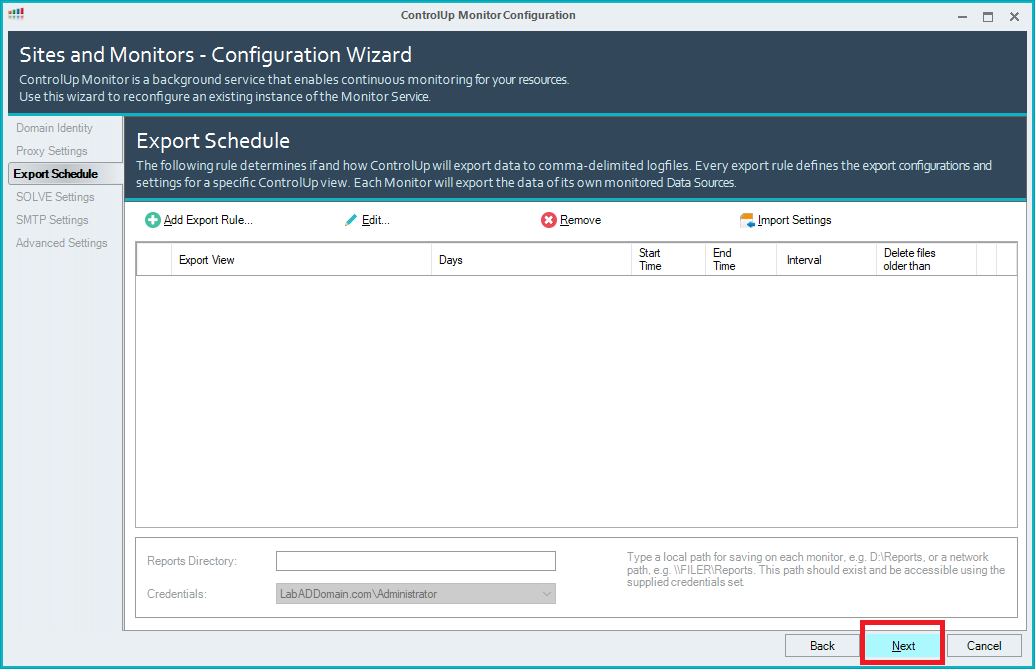
Click Next, as shown in Figure 105.
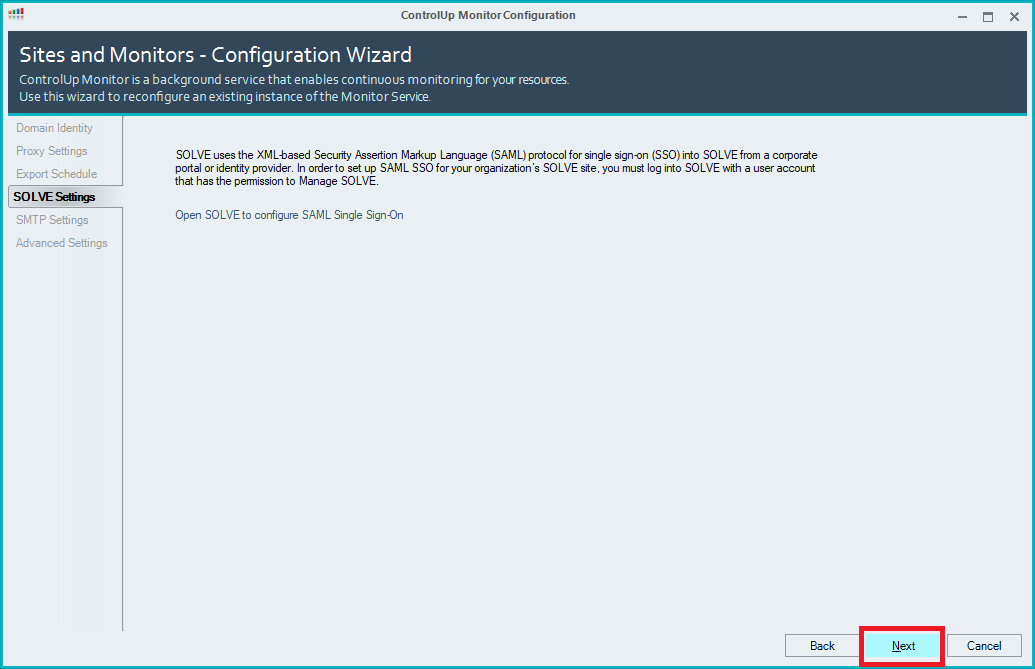
Click Next, as shown in Figure 106.
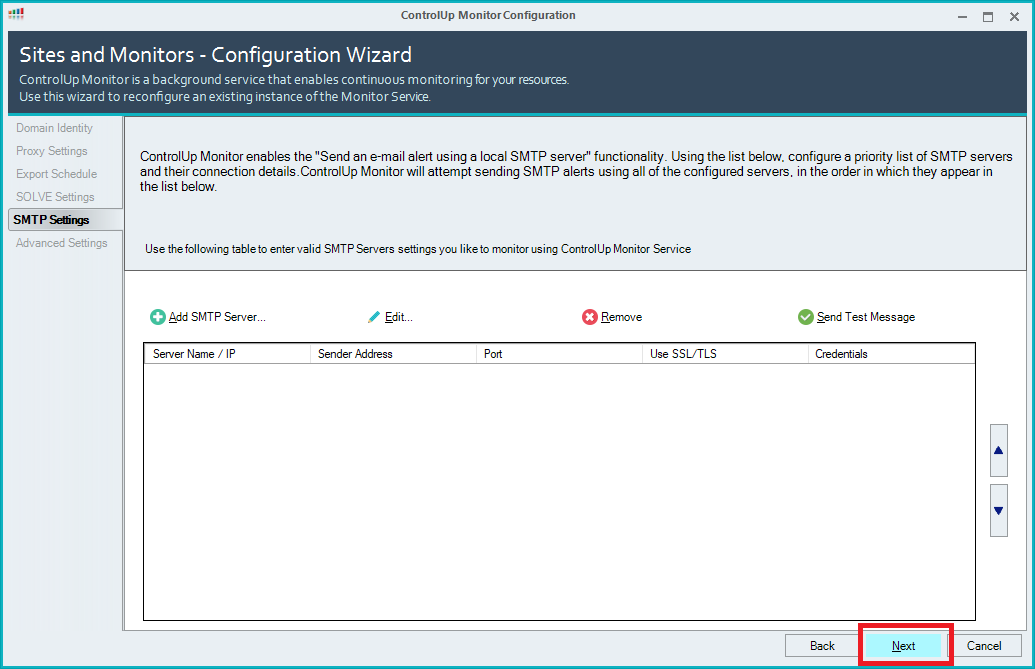
Click Next, as shown in Figure 107.
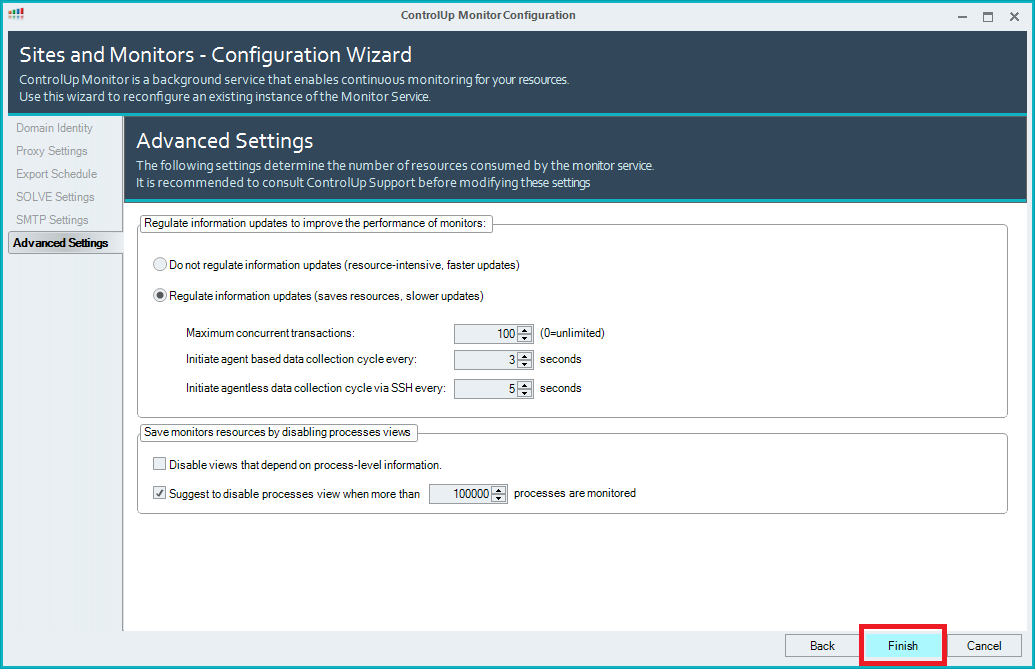
Click Finish, as shown in Figure 108.
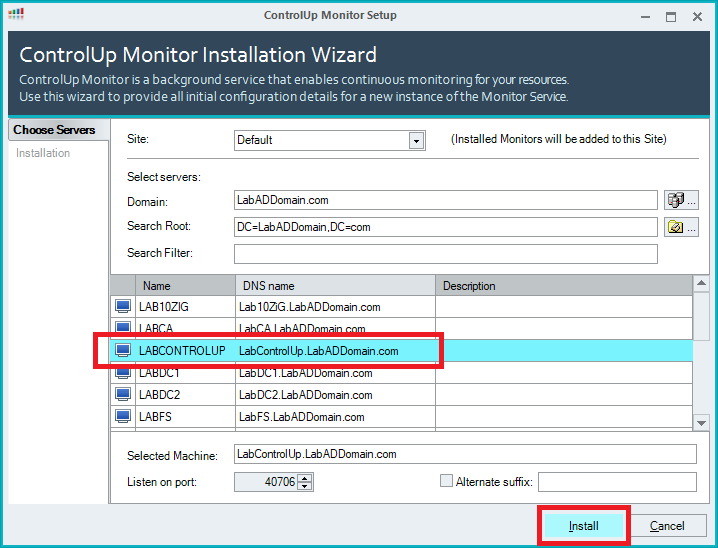
Select the ControlUp server as the Monitor server and click Install, as shown in Figure 109.
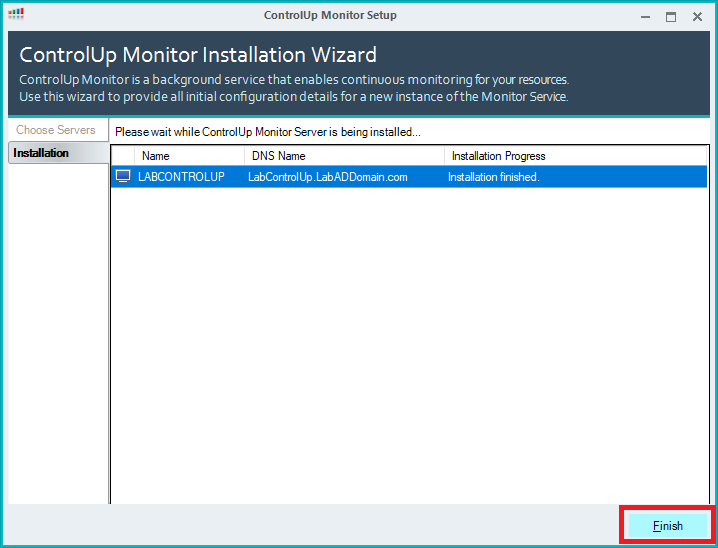
Click Finish, as shown in Figure 110.
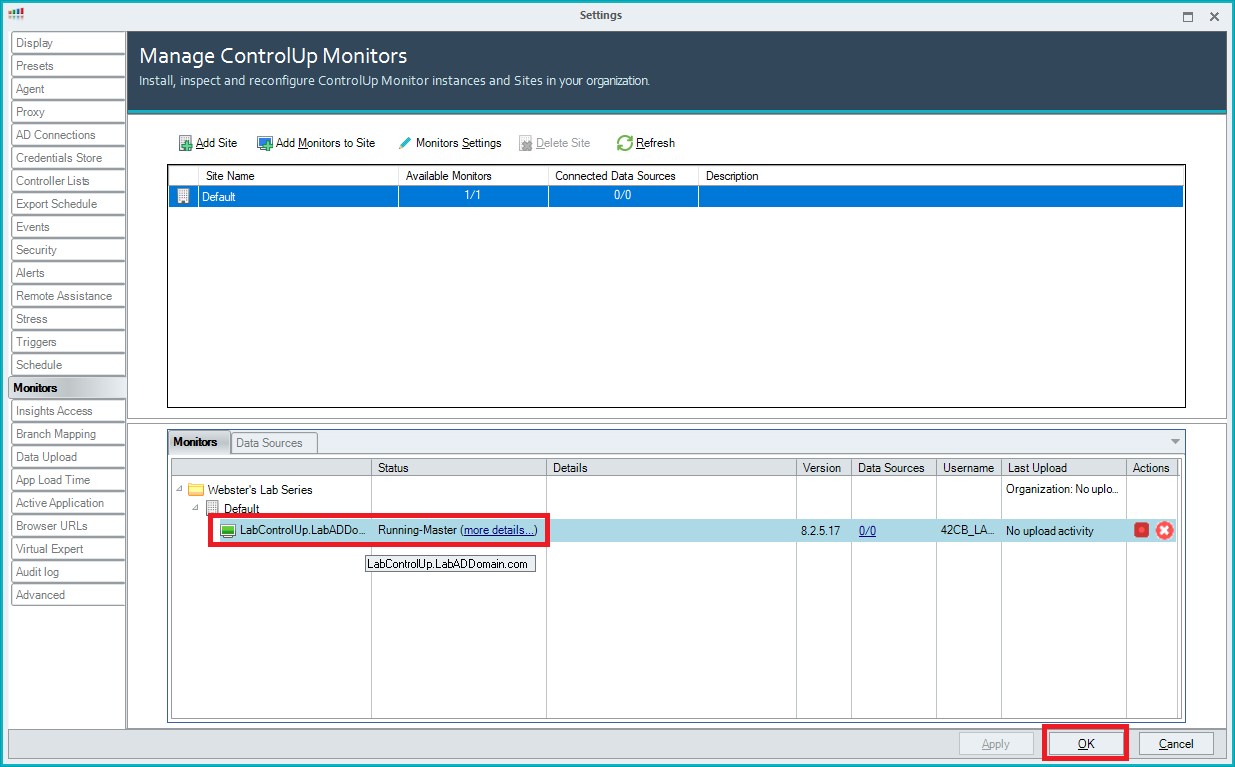
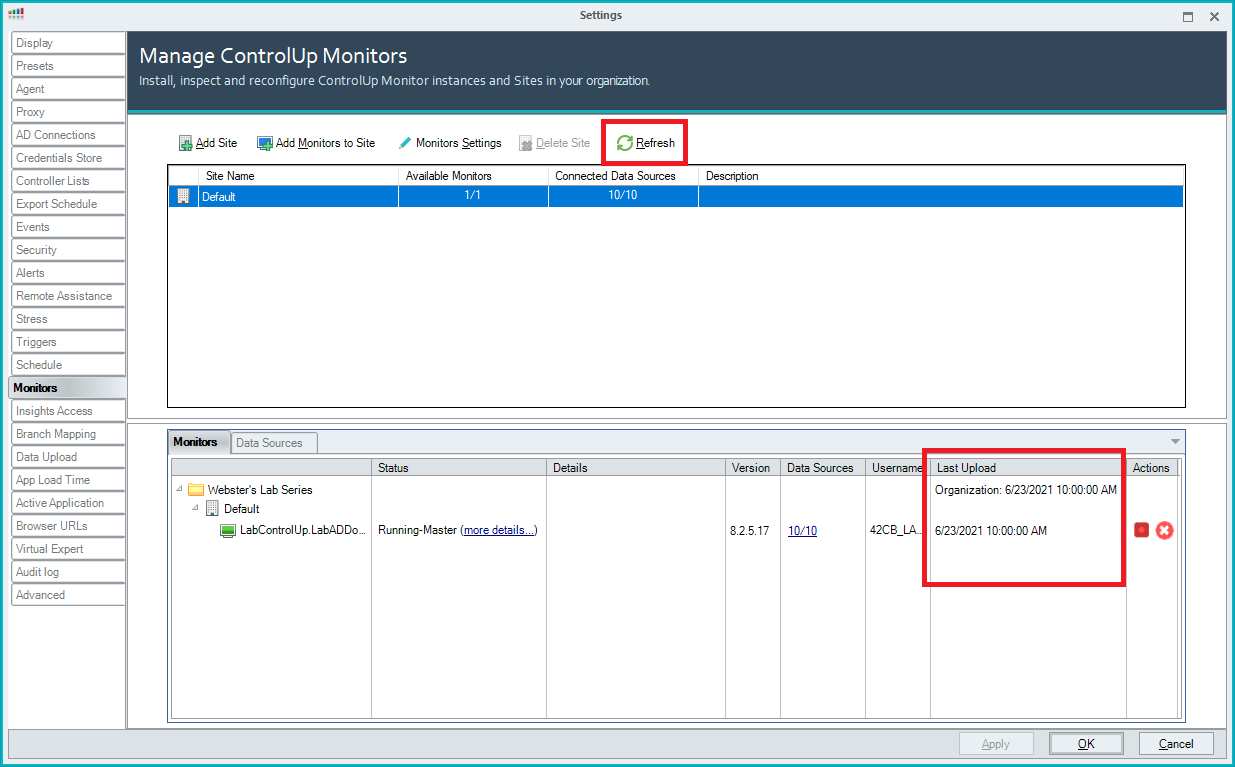
Wait a few minutes, click Refresh, and the Monitor should show Running-Master, as shown in Figure 111. If it doesn’t, either wait a few more minutes or contact ControlUp support.
Click OK.
Create Folders
As in Windows Explorer, Folders in the ControlUp console allow you to organize monitored devices into manageable groups. So far, in this article series, only infrastructure computers exist. Folders allow the grouping of servers by function, action, type, use, or any criteria needed. Folders can mimic an existing AD OU structure or any structure desired.
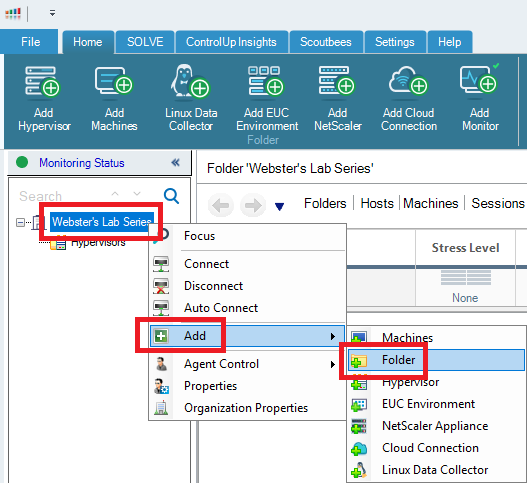
Right-click the Organization Name in the left pane of the ControlUp console, click Add, and click Folder, as shown in Figure 112.
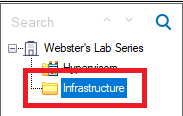
Enter a name for the folder and press Enter, as shown in Figure 113.
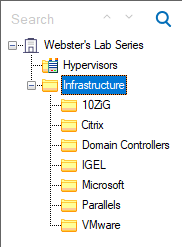
Additional folders can exist at the same level or as sub-folders. I created additional sub-folders to mimic where servers reside in AD, as shown in Figure 114.
Add Hypervisors
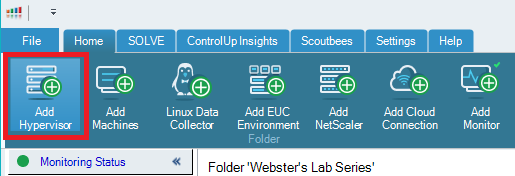
In the toolbar, click Add Hypervisor, as shown in Figure 115.
Enter the following information and click OK, as shown in Figure 116.
- Type = VMware
- URL = https://vCenter.FQDN/sdk (For me, that is https://vCenter.LabADDomain.com/sdk)
- Name = vCenter
- Credentials = From the dropdown list, select the VMware ControlUp account (For me, that is svc_VMwareControlUp
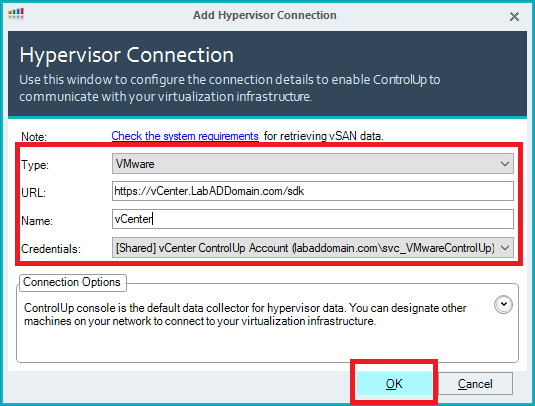
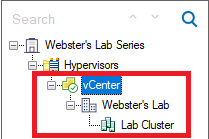
Figure 117 shows vCenter added under the Hypervisors folder.
As shown in Figure 115, click Add Hypervisor.
Enter the following information and click OK, as shown in Figure 118.
- Type = XenServer
- URL = http://XenServerPoolMasterIPAddressorFQDN (For me, that is http://192.168.1.80)
- Name = Automatically filled
- Credentials = From the dropdown list, select the Citrix ControlUp account (For me, that is svc_CitrixControlUp
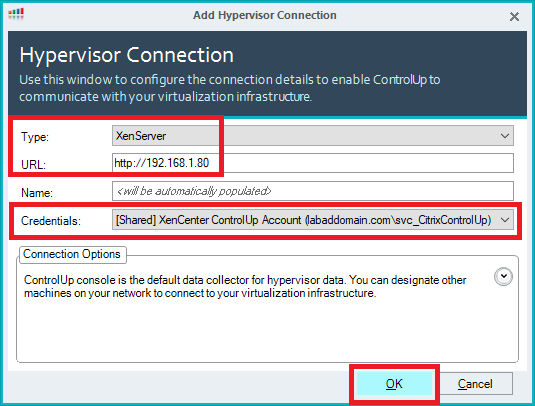
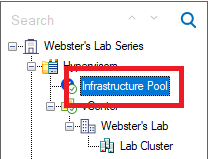
Figure 119 shows the Pool added under the Hypervisors folder.
Add Machines
In my Lab, the XenServer pool holds all my infrastructure VMs.
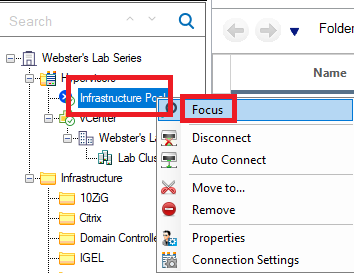
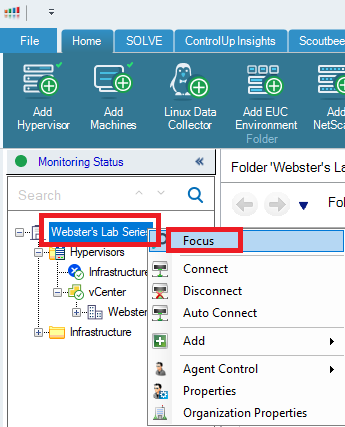
Right-click the hypervisor connection where the infrastructure machines reside and click Focus, as shown in Figure 120.
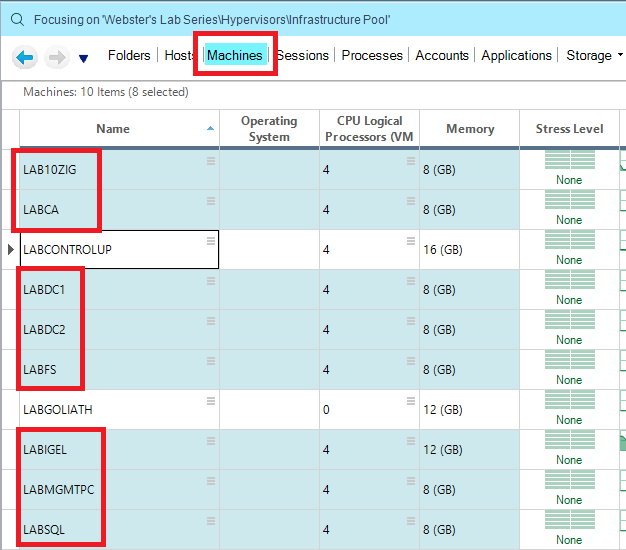
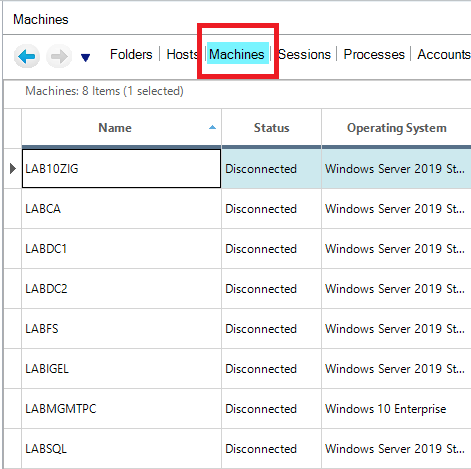
Click on Machines and select the machines to install the ControlUp agent, as shown in Figure 121.
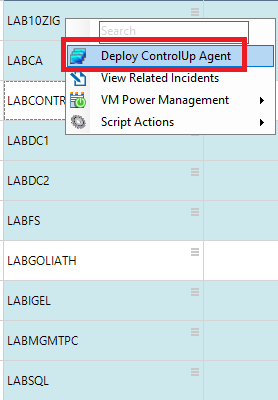
Right-click a selected machine and click Deploy agent, as shown in Figure 122.
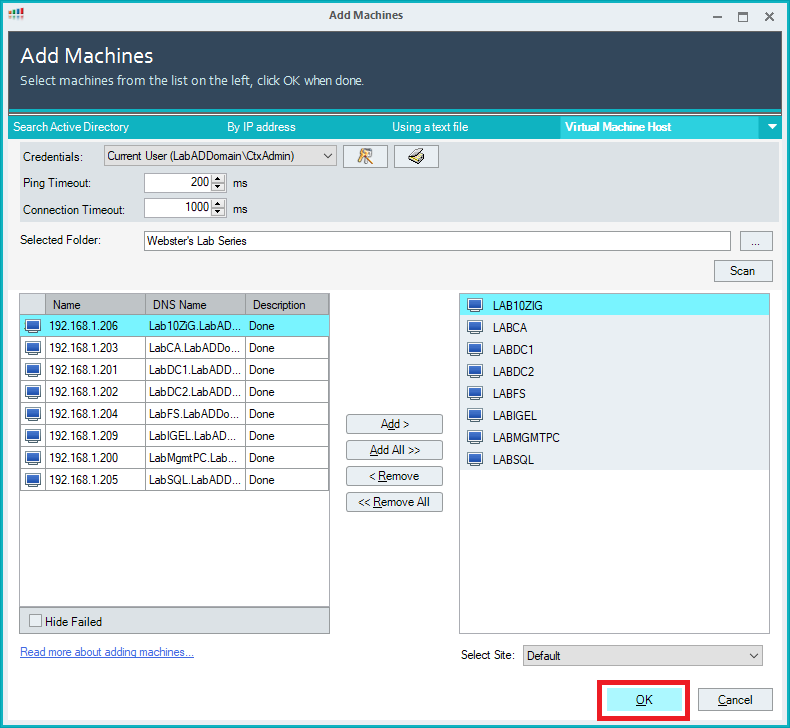
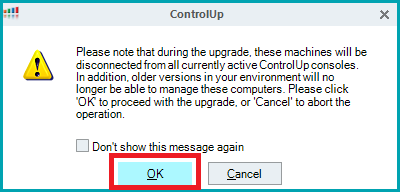
Click OK, as shown in Figure 123.
Click OK, as shown in Figure 124.
As shown in Figure 125, after a few seconds, the selected computers show in the console.
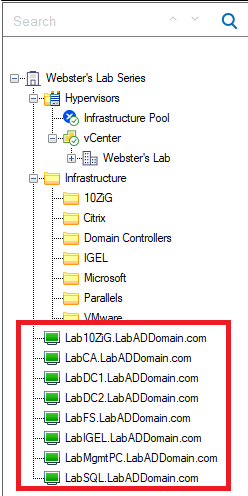
Now that computers are in the console, we can move them to the folders created earlier.
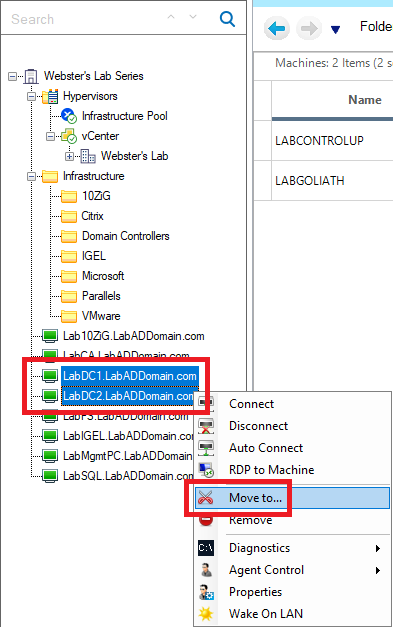
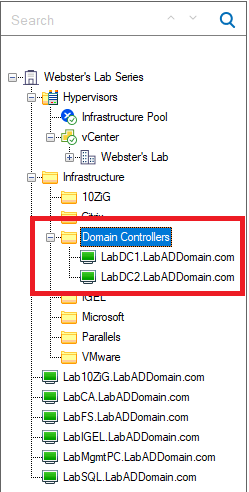
Select the two domain controllers, right-click and click Move to…, as shown in Figure 126.
Expand the top-level folder, select the folder created for the domain controllers, and click OK, as shown in Figure 127.
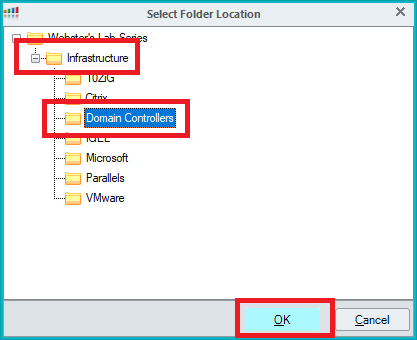
In the list of folders, expand the domain controller’s folder, and the domain controllers are now in their folder, as shown in Figure 128.
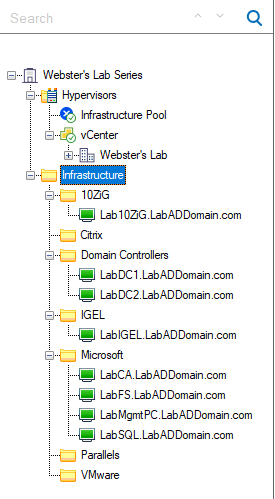
Move the other computers into their folders, as shown in Figure 129. You can also drag and drop computers into folders.
Note: Now that the ControlUp agent is deployed, the temporary Windows Firewall rule, ControlUp Monitored Computer Inbound TCP Ports 49152-65535, can be disabled within the GPMC.
Configure Security
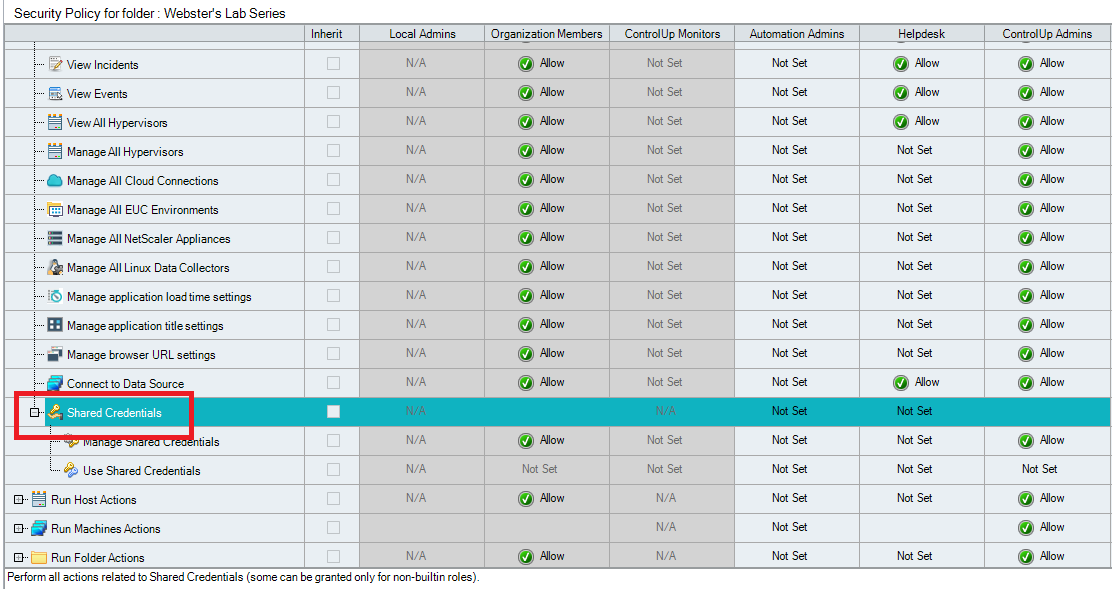
We need to allow others access to the Shared Credentials created when configuring the Monitor and configure our security groups with Admin and Helpdesk access to the console.
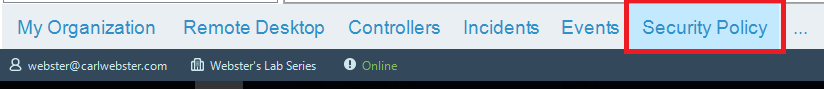
On the bottom of the console, click Security Policy, as shown in Figure 130.
Expand Perform organization-wide actions, as shown in Figure 131.
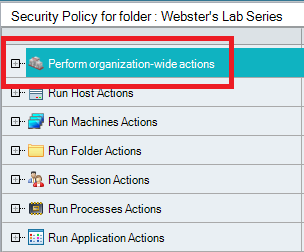
Scroll down and expand Shared Credentials, as shown in Figure 132.
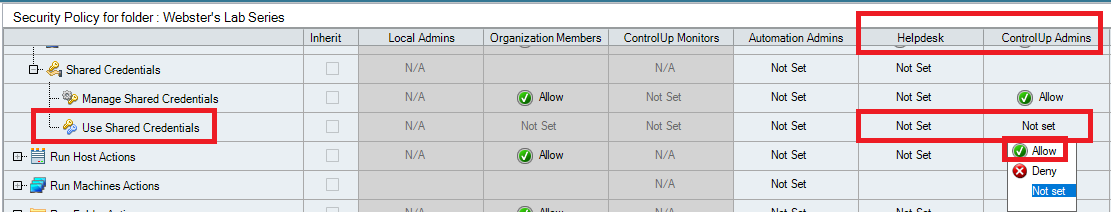
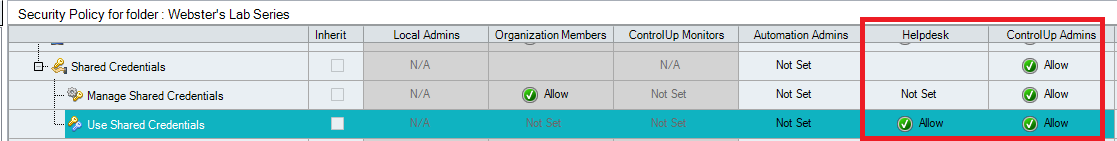
For Use Shared Credentials, in both the Helpdesk and ControlUp Admins columns, click on Not set, and click Allow from the popup, as shown in Figures 133 and 134.
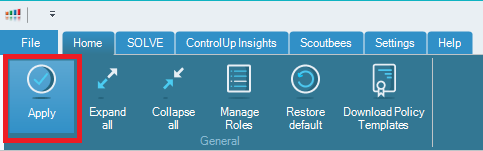
Click Apply, as shown in Figure 135.
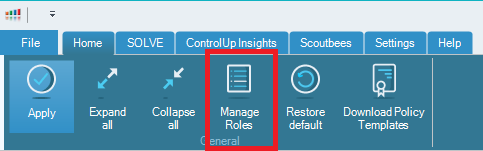
Click Manage Roles, as shown in Figure 136.
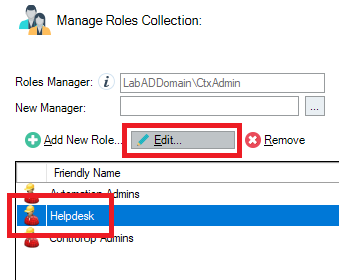
Click Helpdesk and then click Edit, as shown in Figure 137.
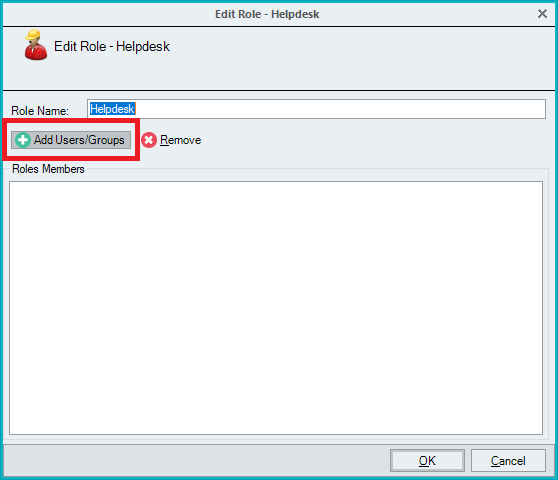
Click Add Users/Groups, as shown in Figure 138.
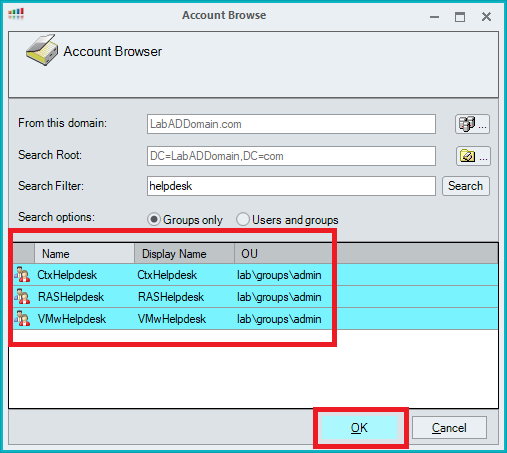
Since the AD security groups created for the helpdesk groups contain “helpdesk”, for the Search Filter, type in helpdesk, click Search, and all the helpdesk security groups appear, as shown in Figure 139.
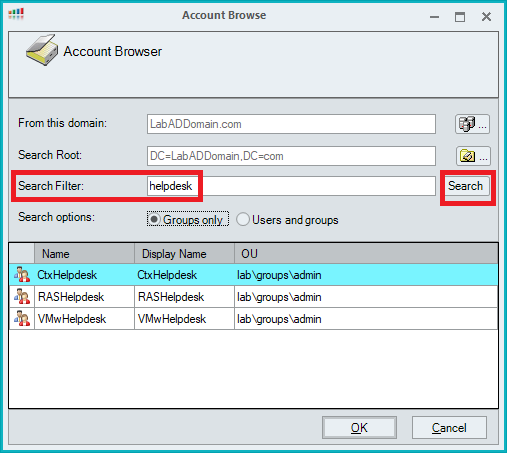
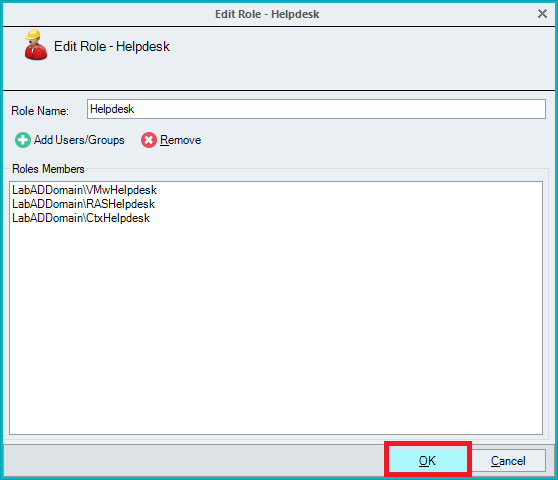
Select all the helpdesk groups and click OK, as shown in Figure 140.
Click OK, as shown in Figure 141.
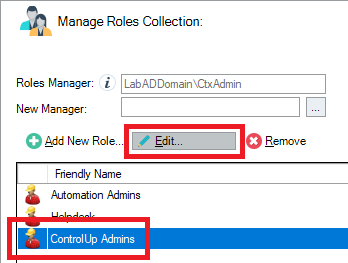
Click ControlUp Admins and then click Edit, as shown in Figure 142.
Click Add Users/Groups, as shown in Figure 143.
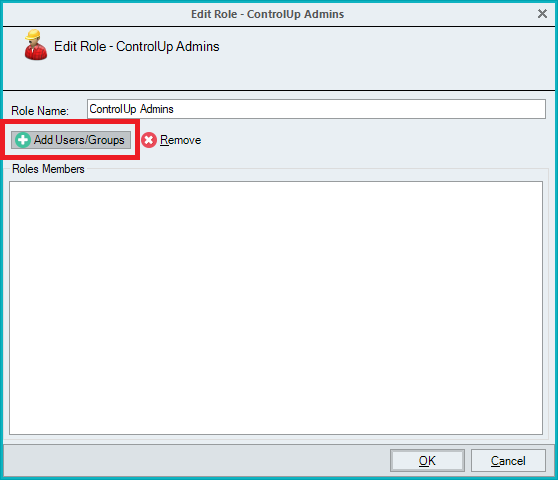
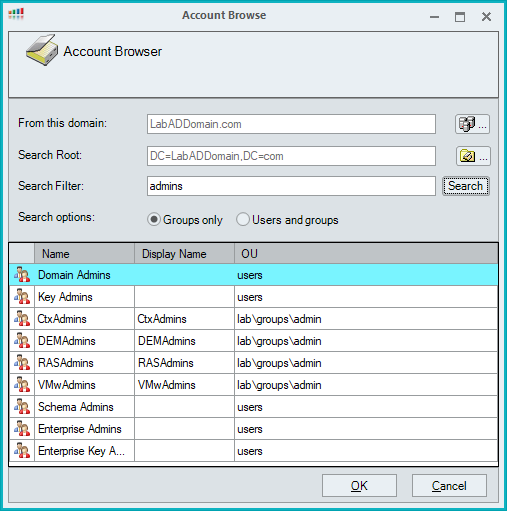
Since the AD security groups created for the admin groups contain “admins”, for the Search Filter, type in admins, click Search, and all the admins security groups appear, as shown in Figure 144.
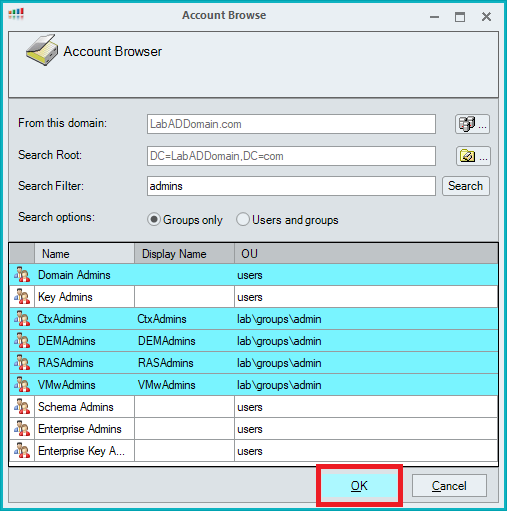
Select the desired groups and click OK, as shown in Figure 145.
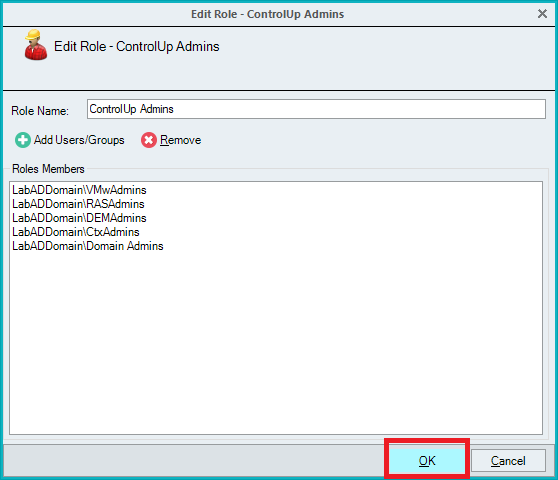
Click OK, as shown in Figure 146.
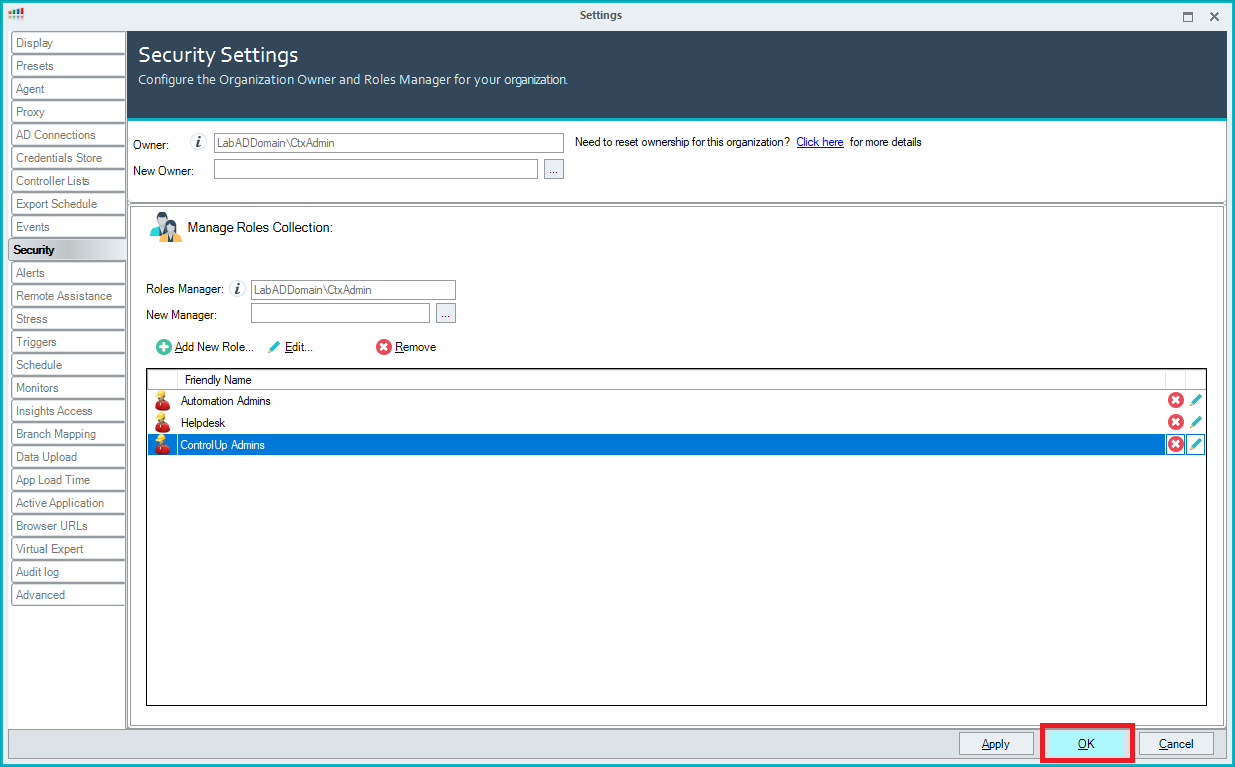
Click OK, as shown in Figure 147.
Verify Monitor Activity
Click My Organization on the bottom of the console, as shown in Figure 148.
Click Monitoring Status, as shown in Figure 149.
Click Refresh, and the Monitor should show a Last Upload status, as shown in Figure 150.
Note: Please see this article on Monitor Alerts from ControlUp if there is no upload activity.
Viewing the Console
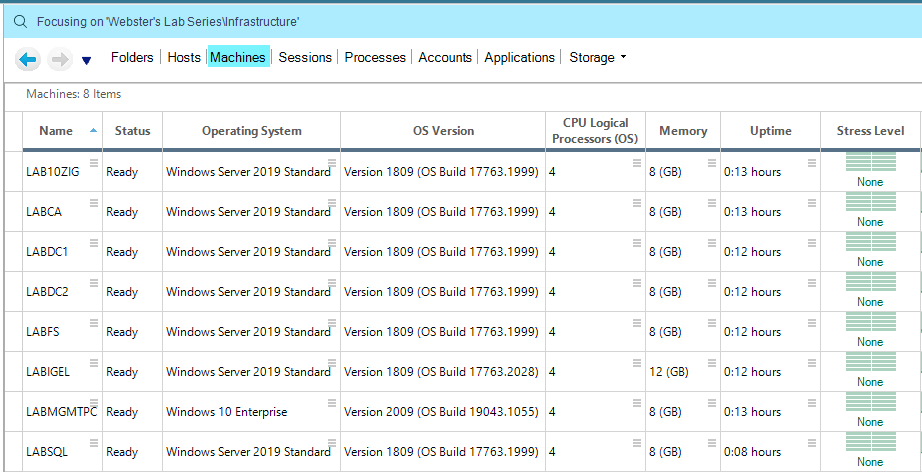
Right-click the Infrastructure folder and click Focus.
What shows is the Default console view for the item in Focus. Figure 151 shows a partial view.
Drag the scroll bar to the far right, and you can see many columns available, as shown in Figure 152.
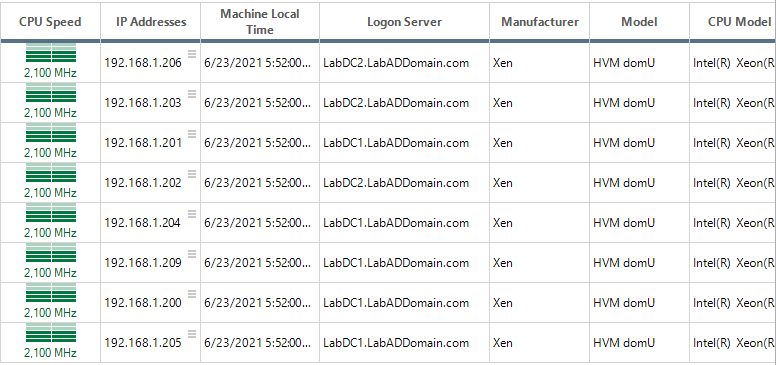
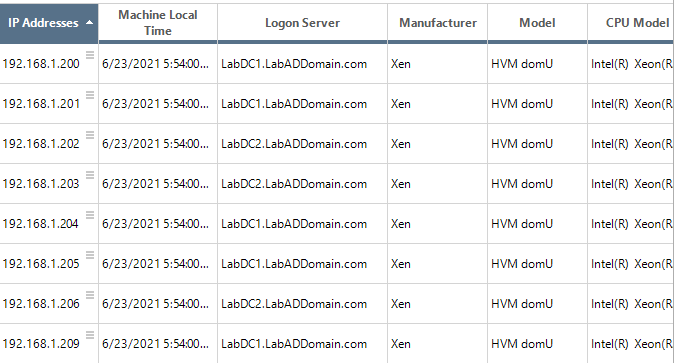
You can sort what you see by any column. For example, double-click the IP Addresses column heading to sort by IP Addresses, as shown in Figure 153.
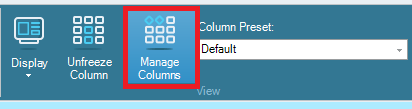
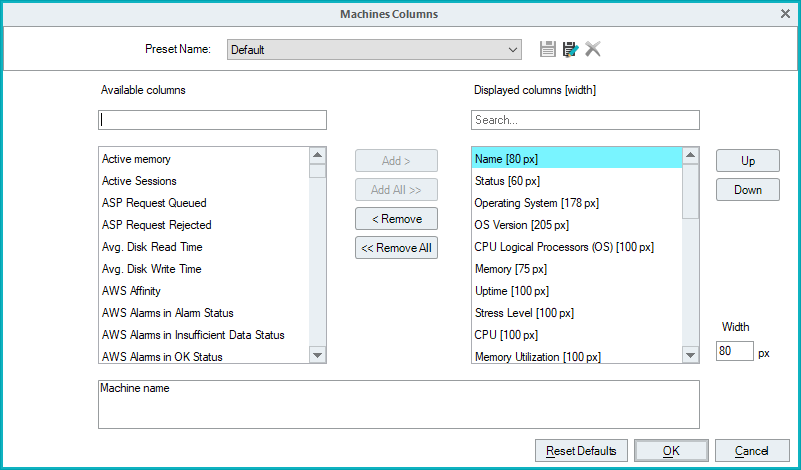
You can add or remove columns from the display by clicking Manage Columns, as shown in Figure 154.
You can add or remove any column(s) you need, as shown in Figure 155.
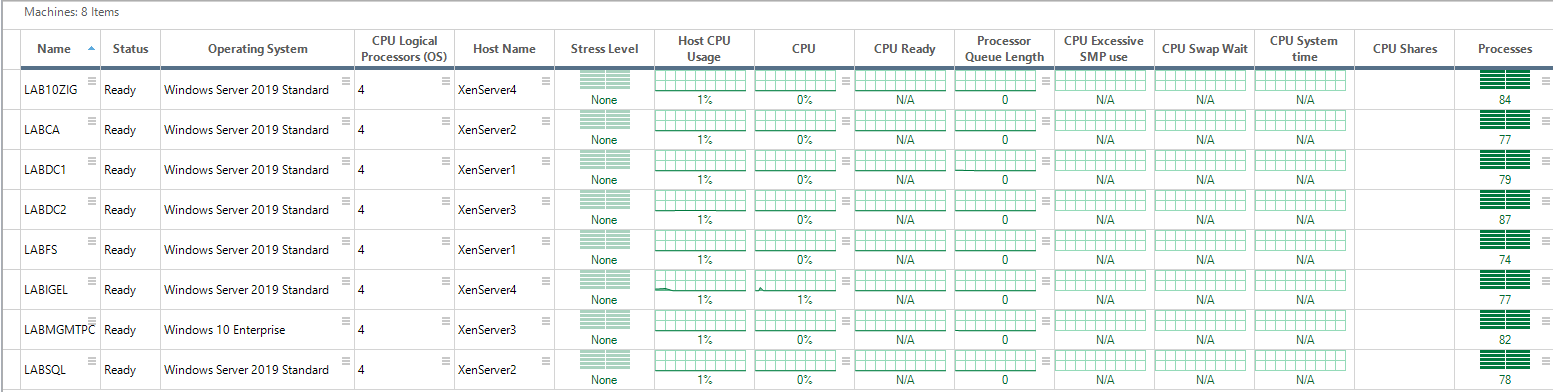
You can also display many ControlUp defined preset column selections by clicking the dropdown Column Preset, as shown in Figure 156.
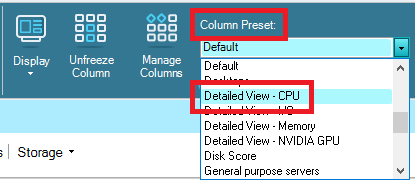
The console display changes to show columns (data) specific to the Preset selected, as shown in Figure 157.
Please schedule time with ControlUp to get a detailed look into what all the ControlUp Real-Time Console can show.
Uninstall Agents on Servers
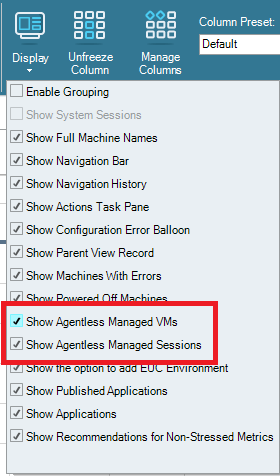
To see only machines with the ControlUp agent, click Display, as shown in Figure 158.
Deselect Show Agentless Managed VMs and Show Agentless Managed Sessions, as shown in Figure 159.
Click on the Organization Name, right-click and select Focus, as shown in Figure 160.
Click Machines, as shown in Figure 161.
To uninstall the agents installed using the console, select the computers with the agents to uninstall, right-click, click Agent Control, and click Uninstall Remote Agent, as shown in Figure 162.
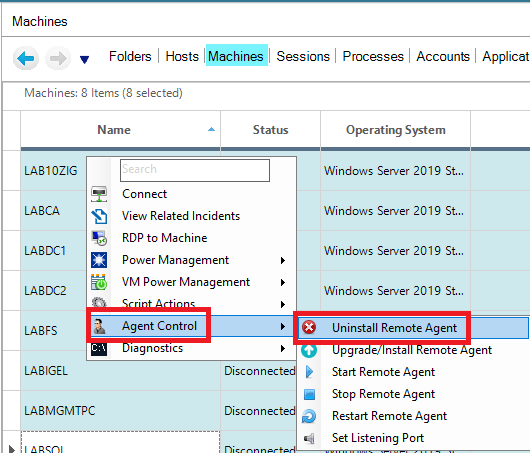
This process uninstalls the agent from the selected computers and removes the selected computers from the ControlUp console, as shown in Figure 163.